“红明谷”杯数据安全大赛 技能场景赛 部分wp
MISC 我的心是冰冰的
描述:似乎有信息被隐藏了。
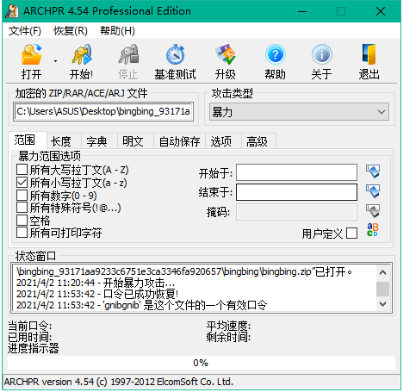
1.首先,思路是盲猜用图中的信息解压缩包的密码
另一边用zip爆破工具爆破,节省时间,爆破居然先爆破出来了
密码是:gnibgnib
2.然后分析bingbing.pcapng
打开后发现是usb键盘流量,或者是usb鼠标流量
网上查资料可得,USB协议的数据部分在Leftover Capture Data域之中,右键leftover capture data –> 应用为列,可以将该域的值在主面板上显示,键盘数据包的数据长度为8个字节,击键信息集中在第3个字节,每次key stroke都会产生一个keyboard event usb packet
可以将 leftover capture data单独提取出来,在linux中,具体命令为:
tshark -r bingbing.pcap -T fields -e usb.capdata > usbdata.txt
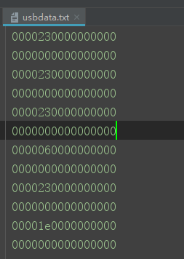
因此,这就是usb键盘流量
3.从得出的userdata.txt文件中过滤出键盘击键相关的流量,并根据映射表,将键盘按键按照对应关系输出出来,查资料找到了网上的脚本
1 #!/usr/bin/env python 2 3 import sys 4 5 import os 6 7 8 9 DataFileName = "usbdata.txt" 10 11 12 13 presses = [] 14 15 16 17 normalKeys = {"04":"a", "05":"b", "06":"c", "07":"d", "08":"e", "09":"f", "0a":"g", "0b":"h", "0c":"i", "0d":"j", "0e":"k", "0f":"l", "10":"m", "11":"n", "12":"o", "13":"p", "14":"q", "15":"r", "16":"s", "17":"t", "18":"u", "19":"v", "1a":"w", "1b":"x", "1c":"y", "1d":"z","1e":"1", "1f":"2", "20":"3", "21":"4", "22":"5", "23":"6","24":"7","25":"8","26":"9","27":"0","28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\t","2c":"<SPACE>","2d":"-","2e":"=","2f":"[","30":"]","31":"\\","32":"<NON>","33":";","34":"'","35":"<GA>","36":",","37":".","38":"/","39":"<CAP>","3a":"<F1>","3b":"<F2>", "3c":"<F3>","3d":"<F4>","3e":"<F5>","3f":"<F6>","40":"<F7>","41":"<F8>","42":"<F9>","43":"<F10>","44":"<F11>","45":"<F12>"} 18 19 20 21 shiftKeys = {"04":"A", "05":"B", "06":"C", "07":"D", "08":"E", "09":"F", "0a":"G", "0b":"H", "0c":"I", "0d":"J", "0e":"K", "0f":"L", "10":"M", "11":"N", "12":"O", "13":"P", "14":"Q", "15":"R", "16":"S", "17":"T", "18":"U", "19":"V", "1a":"W", "1b":"X", "1c":"Y", "1d":"Z","1e":"!", "1f":"@", "20":"#", "21":"$", "22":"%", "23":"^","24":"&","25":"*","26":"(","27":")","28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\t","2c":"<SPACE>","2d":"_","2e":"+","2f":"{","30":"}","31":"|","32":"<NON>","33":"\"","34":":","35":"<GA>","36":"<","37":">","38":"?","39":"<CAP>","3a":"<F1>","3b":"<F2>", "3c":"<F3>","3d":"<F4>","3e":"<F5>","3f":"<F6>","40":"<F7>","41":"<F8>","42":"<F9>","43":"<F10>","44":"<F11>","45":"<F12>"} 22 23 24 25 def main(): 26 27 # check argv 28 29 if len(sys.argv) != 2: 30 31 print "Usage : " 32 33 print " python UsbKeyboardHacker.py data.pcap" 34 35 print "Tips : " 36 37 print " To use this python script , you must install the tshark first." 38 39 print " You can use `sudo apt-get install tshark` to install it" 40 41 print "Author : " 42 43 print " Angel_Kitty <angelkitty6698@gmail.com>" 44 45 print " If you have any questions , please contact me by email." 46 47 print " Thank you for using." 48 49 exit(1) 50 51 52 53 # get argv 54 55 pcapFilePath = sys.argv[1] 56 57 58 59 # get data of pcap 60 61 os.system("tshark -r %s -T fields -e usb.capdata > %s" % (pcapFilePath, DataFileName)) 62 63 64 65 # read data 66 67 with open(DataFileName, "r") as f: 68 69 for line in f: 70 71 presses.append(line[0:-1]) 72 73 # handle 74 75 result = "" 76 77 for press in presses: 78 79 Bytes = press.split(":") 80 81 if Bytes[0] == "00": 82 83 if Bytes[2] != "00": 84 85 result += normalKeys[Bytes[2]] 86 87 elif Bytes[0] == "20": # shift key is pressed. 88 89 if Bytes[2] != "00": 90 91 result += shiftKeys[Bytes[2]] 92 93 else: 94 95 print "[-] Unknow Key : %s" % (Bytes[0]) 96 97 print "[+] Found : %s" % (result) 98 99 100 101 # clean the temp data 102 103 os.system("rm ./%s" % (DataFileName)) 104 105 106 107 108 109 if __name__ == "__main__": 110 111 main()
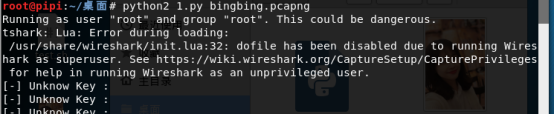

最后结果从<DEL>分段分别解密文, 16进制解码即可
flag值: flag{8f9ed2f933ef14a8d0523d0349e1299c}
总结:挺有劲儿的一题,做了好久,明明答案早已经出来了,开始却没发现那是16进制,辗转了好久,以为是脚本错了,折腾好久,最后才想到答案可能是密文,提交答案时却是第10名提交的,错失前三血
MISC 签到
答对8道数据安全知识小竞赛题,得flag

flag值: flag{7e63095d-4310-4f24-a01a-4a858d442fab}
赛后感受:题目好多不会做,还是很自闭了,感谢队友的辅助,一起加油!



 浙公网安备 33010602011771号
浙公网安备 33010602011771号