KMS的几个开源实现汇总
搜索关键词
open source key management server
“key management server”
KMIP
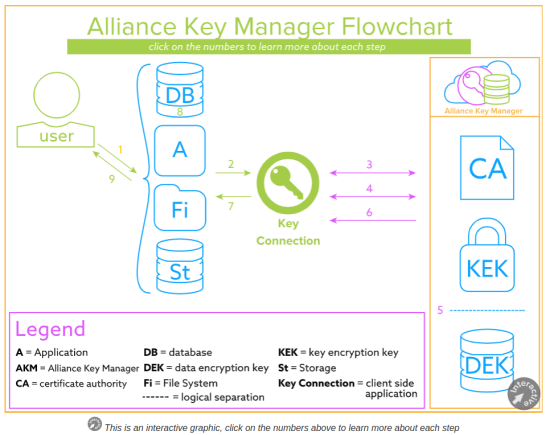
集中密钥工作流程
https://www.townsendsecurity.com/products/centralized-encryption-key-management
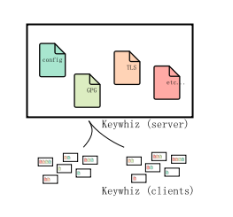
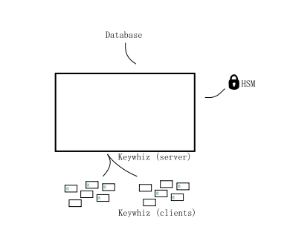
Keywhiz
https://square.github.io/keywhiz/
https://gitee.com/mirrors/keywhiz/tree/master
Keywhiz makes managing secrets easier and more secure. Keywhiz servers in a cluster centrally store secrets encrypted in a database. Clients use mutually authenticated TLS (mTLS) to retrieve secrets they have access to. Authenticated users administer Keywhiz via CLI. To enable workflows, Keywhiz has automation APIs over mTLS.
Keywhiz 是管理和分配隐私信息的系统,适用于面向服务的架构(SOA)。
每个组织的服务或者系统都要求有密码或者其他的隐私信息:
TLS 认证或者密钥
GPG 密钥
API tokens
数据库证书
通常是把隐私信息放到配置文件,代码的后面,还有就是复制文件放到服务器以外的地方。前者容易泄漏,后者很难追踪。
Keywhiz 提供了一个简单而又安全的方式来管理这些隐私信息。Keywhiz 服务器在集中的集群中存储这些信息,数据库加密后存储。客户端使用TLS(mTLS) 来访问那些信息。认证用户通过 CLI 或者 web app UI 管理 Keywhiz。为了使用工作流,Keywhiz 基于 mTLS自动化 APIs,支持简单的隐私信息生成插件。
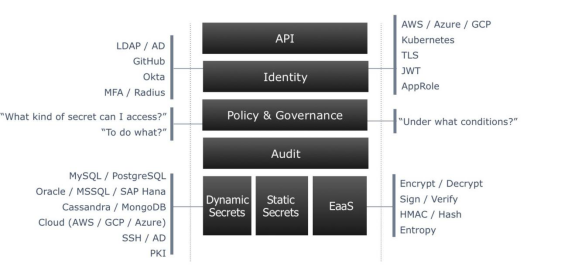
Vault
https://learn.hashicorp.com/vault
HashiCorp Vault作为集中化的私密信息管理工具,具有以下特点:
存储私密信息。 不仅可以存放现有的私密信息,还可以动态生成用于管理第三方资源的私密信息。所有存放的数据都是加密的,任何动态生成的私密信息都有租期,并且到期会自动回收。
滚动更新密钥。用户可以随时更新存放的私密信息。Vault提供了加密即服务(encryption-as-a-service)的功能,可以随时将密钥滚动到新的密钥版本,同时保留对使用过去密钥版本加密的值进行解密的能力。 对于动态生成的秘密,可配置的最大租赁寿命确保密钥滚动易于实施。
审计日志。 保管库存储所有经过身份验证的客户端交互的详细审核日志:身份验证,令牌创建,私密信息访问,私密信息撤销等。 可以将审核日志发送到多个后端以确保冗余副本。
另外,HaishiCorp Vault提供了多种方式来管理私密信息。用户可以通过命令行、HTTP API等集成到应用中来获取私密信息。
作者:ThoughtWorks
链接:https://www.jianshu.com/p/f34bf6ee3ac3
来源:简书
著作权归作者所有。商业转载请联系作者获得授权,非商业转载请注明出处。
https://zhuanlan.zhihu.com/p/69971600 Hashicorp vault 简明配置教程
http://jiagoushi.pro/adopting-hashicorp-vault-day-zero
KLMS KMIP
KLMS over KMIP is good and easy to use solution for key management. This is an open source solution written in Java. See the below link for reference. http://www.ibm.com/developerworks/library/se-kmip4j/
The package named stubInterface will contains all the api required to use KLMS over KMIP.
KLMS: Key Lifecycle Management Systems
KMIP: Key Management Interoperability Protocol

PyKMIP
https://github.com/OpenKMIP 开源实现
PyKMIP is a Python implementation of the Key Management Interoperability Protocol (KMIP), an OASIS communication standard for the management of objects stored and maintained by key management systems. KMIP defines how key management operations and operation data should be encoded and communicated between client and server applications. Supported operations include the full CRUD key management lifecycle, including operations for managing object metadata and for conducting cryptographic operations. Supported object types include:
symmetric/asymmetric encryption keys
passwords/passphrases
certificates
opaque data blobs, and more
https://hub.docker.com/r/jzendle/kmip-server
客户端的几个命令例子
.. py:method:: create(algorithm, length, operation_policy_name=None, name=None, cryptographic_usage_mask=None)
Create a symmetric key on a KMIP appliance.
.. py:method:: create_key_pair(algorithm, length, operation_policy_name=None, public_name=None, public_usage_mask=None, private_name=None, private_usage_mask=None)
Create an asymmetric key pair on a KMIP appliance.
.. py:method:: decrypt(data, uid=None, cryptographic_parameters=None, iv_counter_nonce=None)
Decrypt data using the specified decryption key and parameters.
.. py:method:: delete_attribute(unique_identifier=None, **kwargs)
Delete an attribute from a managed object.
.. py:method:: encrypt(data, uid=None, cryptographic_parameters=None, iv_counter_nonce=None)
Encrypt data using the specified encryption key and parameters.
.. py:method:: get(uid=None, key_wrapping_specification=None)
Get a managed object from a KMIP appliance.
.. py:method:: get_attributes(uid=None, attribute_names=None)
Get the attributes associated with a managed object.
keytransparency
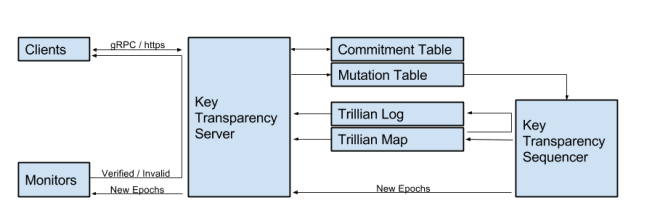
https://gitee.com/mirrors_google/keytransparency/blob/master/docs/design.md
Scenarios
Key Transparency ensures, with mathematical certainty, that account owners can see all the public keys that have been used to authenticate their account or send them messages.
This assured-system architecture is useful in a variety of scenarios from end-to-end encryption to enterprise account management. Any scenario that involves authenticating users with public keys (eg. U2F) can significantly benefit from Key Transparency.
|
Scenario |
Description |
|
Encrypted Messaging |
Key Transparency is ideal for user friendly end-to-end encrypted messaging. By making key management analogous to device management, users do not have to learn any new concepts, and no additional UI beyond device management is needed. Key management fits seamlessly into existing account life-cycle flows, and users are protected without requiring them to take additional actions. |
|
Encrypted Storage |
Key Transparency can also be used to securely rotate the keys used for encrypted storage systems such as upspin.io |
|
PGP Encrypted Email |
Key Transparency was initially built to solve the problem of public key lookup for PGP email encryption. KT has the potential to make PGP significantly more usable than the existing web-of-trust model. |
|
Insider Risk |
Key Transparency removes the ability of privileged users to modify other user accounts without detection. This protects the privileged user from manipulation and ensures system safety even if the privileged user's account is compromised. |
|
Post Compromise Security Audit |
By relying on mathematics, Key Transparency significantly reduces the trusted computing base (TCB) of an authentication system. This makes reasoning about the security properties of an enterprise under attack much easier. The system administrator can have certainty that the authentication records for all accounts are intact, and that users will be able to quickly correct any account compromise. |
|
Cloud Adoption |
By employing a zero-trust architecture, Key Transparency provides efficient evidence to relying parties that the authentication system is operating correctly on an ongoing basis. This can increase cloud product adoption by removing one system from the list of systems that are difficult for customers to audit and control. |
使用场景例子upspin.io
To illustrate the relationship between these components, here is the sequence of requests a client exchanges with the servers to read the file augie@upspin.io/Images/Augie/large.jpg:
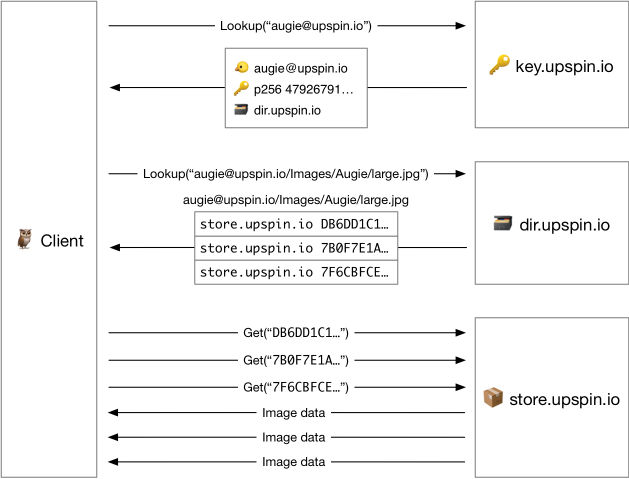
The client asks the key server for the record describing the owner of the file, which is the user name at the beginning of the file name (augie@upspin.io). The key server’s response contains the name of the directory server holding that user’s tree (dir.upspin.io) and Augie’s public key.
The client asks the directory server for the directory entry describing the file. The response contains a list of block references, which include the name of the store server (store.upspin.io).
The client can then ask the store server for each of the blocks, pipelining the requests for efficiency.
The client decrypts the blocks (using Augie’s public key) and concatenates them to assemble the file.
https://upspin.io/doc/security.md
As far as Upspin is concerned, a user is an email address, authenticated by an elliptic curve key pair used for signing and encrypting. We anticipate that the user will rotate keys over time, but we also assume that they will retain all old key pairs for use in decrypting old content, and will accept losing that access to that content if they lose all copies of their keys.
密钥轮换
|
upspin cmd operation |
public,secret.upspinkey |
secret2.upspinkey |
keyserver |
signatures |
wraps |
|
initial key |
k1 |
- |
k1 |
k1, - |
k1 |
|
new key |
k2 |
k1 |
k1 |
k1, - |
k1 |
|
countersign |
k2 |
k1 |
k1 |
k2, k1 |
k1 |
|
rotate |
k2 |
k1 |
k2 |
k2, k1 |
k1 |
|
share -fix |
k2 |
k1 |
k2 |
k2, k1 |
k2 |
K8S的kms
https://kubernetes.io/zh/docs/tasks/administer-cluster/kms-provider/
KMS 加密驱动使用封套加密模型来加密 etcd 中的数据。 数据使用数据加密密钥(DEK)加密;每次加密都生成一个新的 DEK。 这些 DEK 经一个密钥加密密钥(KEK)加密后在一个远端的 KMS 中存储和管理。 KMS 驱动使用 gRPC 与一个特定的 KMS 插件通信。这个 KMS 插件作为一个 gRPC 服务器被部署在 Kubernetes 主服务器的同一个主机上,负责与远端 KMS 的通信。
Hadoop KMS / Ranger KMS
Ranger KMS is based on Hadoop KMS developed by the Apache community. The main difference between Hadoop KMS and Ranger KMS is that the Hadoop KMS stores keys in a file-based Java keystore where as Ranger allows you to store keys in a secure database. The centralized administration of the Ranger KMS is provided through the Ranger admin portal.
There are three main functions within the Ranger KMS: Key management, Access control policies for key management, and audit. To know how to set up and configure Ranger KMS, visit our knowledge center.
https://www.pianshen.com/article/2354126360/
Ranger KMS加密HDFS的配置和权限设置

